Difference between revisions of "Journal:Digital transformation risk management in forensic science laboratories"
Shawndouglas (talk | contribs) (Saving and adding more.) |
Shawndouglas (talk | contribs) (Saving and adding more.) |
||
| Line 158: | Line 158: | ||
===Automation complexity and pitfalls=== | ===Automation complexity and pitfalls=== | ||
In forensic contexts, use of automated systems, including those with AI and [[machine learning]] (ML), support analysis performed by human specialists who interpret the results. Although such automation can help maintain consistency and increase efficiency in forensic analysis, there are several major limitations that must be guarded against. Automated systems can have bugs that produce incorrect results, which can have serious consequences in a forensic context.<ref name="MurrayQueens15">{{cite web |url=https://www.couriermail.com.au/news/queensland/queensland-authorities-confirm-miscode-affects-dna-evidence-in-criminal-cases/news-story/833c580d3f1c59039efd1a2ef55af92b |title=Queensland authorities confirm ‘miscode’ affects DNA evidence in criminal cases |author=Murray, D. |work=The Courier Mail |date=20 March 2015}}</ref> Additionally, automated AI/ML systems can introduce bias due to poorly selected training datasets, and can lead to misinterpretations when the results are not fully understood.<ref name="MargagliottiMachine19">{{cite journal |title=Machine learning & forensic science |journal=Forensic Science International |author=Margagliotti, G.; Bollé, T. |volume=298 |pages=138–39 |year=2019 |doi=10.1016/j.forsciint.2019.02.045}}</ref> When automated AI/ML systems are used to support investigation and forensic analysis, such as comparison of faces in digital video or photographs, algorithmic false positives can lead to incorrect results. | In forensic contexts, use of automated systems, including those with AI and [[machine learning]] (ML), support analysis performed by human specialists who interpret the results. Although such automation can help maintain consistency and increase efficiency in forensic analysis, there are several major limitations that must be guarded against. Automated systems can have bugs that produce incorrect results, which can have serious consequences in a forensic context.<ref name="MurrayQueens15">{{cite web |url=https://www.couriermail.com.au/news/queensland/queensland-authorities-confirm-miscode-affects-dna-evidence-in-criminal-cases/news-story/833c580d3f1c59039efd1a2ef55af92b |title=Queensland authorities confirm ‘miscode’ affects DNA evidence in criminal cases |author=Murray, D. |work=The Courier Mail |date=20 March 2015}}</ref> Additionally, automated AI/ML systems can introduce bias due to poorly selected training datasets, and can lead to misinterpretations when the results are not fully understood.<ref name="MargagliottiMachine19">{{cite journal |title=Machine learning & forensic science |journal=Forensic Science International |author=Margagliotti, G.; Bollé, T. |volume=298 |pages=138–39 |year=2019 |doi=10.1016/j.forsciint.2019.02.045}}</ref> When automated AI/ML systems are used to support investigation and forensic analysis, such as comparison of faces in digital video or photographs, algorithmic false positives can lead to incorrect results. | ||
====Reliability and human rights concerns scenario==== | |||
In this scenario, an independent study of six facial recognition technology test deployments performed by the London Metropolitan Police Service (MPS) found a high number of false positives. In total, only eight out of 46 automatically generated potential face recognition “matches” that were considered and evaluated by a human were deemed to be correct. The eight verified correct matches were determined by some form of confirmation such as through a street-based identity check.<ref name="FusseyIndep19">{{cite web |url=http://repository.essex.ac.uk/24946/ |title=Independent Report on the London Metropolitan Police Service’s Trial of Live Facial Recognition Technology |author=Fussey, P.; Murray, D. |publisher=University of Essex Human Rights Centre |date=2019}}</ref> The study paid particular attention to the risks of such technology interfering with fundamental human rights, including privacy violations and discrimination due to algorithmic bias relating to sex, race, or ethnicity. | |||
This study highlights the fact that any automated system can have some false positives and false negatives, which demands that human analysts are in the loop to manage the risks of something important being overlooked or misinterpreted. Good practice here can also help deal with the risk of contextual bias. An automated system supporting forensic analysis should offer sequential unmasking capabilities.<ref name="KopplStrat19">{{cite journal |title=Strategic choice in linear sequential unmasking |journal=Science & Justice |author=Koppl, R. |volume=59 |issue=2 |pages=166-171 |year=2019 |doi=10.1016/j.scijus.2018.10.010}}</ref> | |||
Ultimately, automated systems supporting forensic analysis should integrate forensic requirements, risk management, and privacy, i.e., forensic-by-design. If a system is forensic-by-design, forensic preparedness principles and practices have been integrated into the system engineering lifecycle, including risk management, incident handling, forensic principles, and legal compliance.<ref name="RahmanForensic16">{{cite journal |title=Forensic-by-Design Framework for Cyber-Physical Cloud Systems |journal=IEEE Cloud Computing |author=Rahman, N.H.A.; Glisson, W.B.; Yang, Y. et al. |volume=3 |issue=1 |pages=50–59 |year=2016 |doi=10.1109/MCC.2016.5}}</ref> However, such forensic-by-design is not common practice at the moment, and there are growing concerns about the unreliability and invasiveness of such technologies for criminal investigation purposes. Some cities in California are strictly controlling the acquisition and utilization of "any software, electronic device, system utilizing an electronic device, or similar device used, designed, or primarily intended to collect, retain, process, or share audio, electronic, visual, location, thermal, biometric, olfactory or similar information specifically associated with, or capable of being associated with, any individual or group."<ref name="SFCountyOrdinance19">{{cite web |url=https://sfbos.org/sites/default/files/o0107-19.pdf |format=PDF |title=Administrative Code - Acquisition of Surveillance Technology, Ordinance No. 107-19 |publisher=County of San Francisco |date=21 May 2019}}</ref> | |||
Forensic laboratories must be prepared to address concerns about reliability, privacy, and discrimination associated with use of technology for processing data, particularly AI/ML systems for data analysis. | |||
==Digital reinforcement of forensic science principles== | |||
Core principles and processes in forensic laboratories can be bolstered using technology while increasing the efficiency and quality of services. These core principles include authenticity and integrity; reliability and reproducibility; and quality and efficiency. In addition, intelligent application of digital technology can create new opportunities to deal with crime in digitalized society. | |||
===Authenticity and integrity=== | |||
Digital transformation of forensic laboratories can enhance the traceability of traces. Existing computerized systems for processing physical and digital evidence typically provide a digital audit trail and its treatment throughout its lifecycle in the forensic laboratory. Alterations to data files (raw and processed) might be detectable using the digital traces that are created routinely during the processing of exhibits in a forensic laboratory. In some situations, to authenticate data files and associated results, it is necessary to perform contextual analysis, including digital forensic analysis of the original data and metadata. | |||
===Contextual reconstruction scenario=== | |||
In this scenario, questions have arisen about the results of some samples processed by a laboratory. In order to assess the reported results, the raw data was recovered from analysis systems along with processed results. The information from these files was compared with details recorded in the LIMS, and discrepancies were found. However, audit logs in the LIMS were found that corresponded with the original data. Timestamps of the original data files and the LIMS were also examined to determine contemporaneous activities versus later changes. | |||
As this scenario highlights, it is advisable not to leave evidence authentication to chance. With properly protected audit trail and data file integrity mechanisms (preferably automated), a digitalized chain of custody can be maintained from evidence intake to evidence return or archiving, providing valuable insights into laboratory operations and helping protect against undetected mistakes and forensic fraud. Some forensic laboratories have adopted bar code scanning and RFID labels to mark and track exhibits throughout their lifecycle. Some forensic laboratories use secure storage to retain raw data files. Some laboratories are developing enhanced methods for maintaining provenance information using blockchain-based systems.<ref name="BurriChrono20" /><ref name="Jaquet-ChiffelleTamper20" /> | |||
With such automated provenance tracking mechanisms in place, every deliverable that a forensic laboratory produces could include the associated electronic chain of custody details as an appendix to demonstrate proper handling. Providing this provenance information in a standardized format such as [https://caseontology.org/ CASE] enables receiving organizations to integrate the information into their information management systems and detect potential inconsistencies more easily, and even automatically. | |||
===Reliability and reproducibility=== | |||
Forensic science practices demand that the data, methods, tools, and analysis are described in sufficient detail that they can be carried out again with the same results. | |||
Digital transformations can support reproducibility of processing by documenting all phases of the evidence lifecycle in the forensic laboratory, as well as reproducibility of analysis by providing others with original data to perform independent analysis. Some software developers also provide a standalone application for viewing the results of forensic processes, enabling others to verify forensic analysis without requiring them to purchase licenses for the specific software and/or version. | |||
====Reproducibility of forensic analysis scenario==== | |||
In this scenario, multiple parties need to perform an in-depth review of the results produced by a forensic laboratory, as part of an investigation involving various computers and mobile devices. To save cost and time, the forensic laboratory provided the multiple parties with a complete package of data and viewing software necessary to perform in-depth review. Using this approach, all parties could assess the reliability of the evidence and results without having to purchase specialized equipment and software, or to run time consuming data processing operations that had already been performed by the laboratory. | |||
This scenarion shows that expanding decentralisation of forensic capabilities is driving the need for data and analysis results to be transferred securely between systems and organizations that is fully traceable, if not completely repeatable. This trend raises the importance of international standards for harmonization of forensic methods and data formats. | |||
===Quality and efficiency=== | |||
Technological advances enable forensic laboratories to process evidence more quickly while maintaining quality. Forensic laboratories can manage the systems that they rely on for processing evidence in order to standardize the processing and output. The National Institute of Standards and Technology (NIST) Computer Forensic Tool Testing (CFTT) program publishes open access test reports for software commonly used in digital forensic laboratories, detailing both capabilities and limitations. The European Network of Forensic Science Institutes (ENFSI) and the US DoD Cyber Crime Center (DC3) also perform tool validation and testing, and provide the results to law enforcement agencies. Similar validation and testing should be applied to computers and software used to operate traditional forensic equipment. As with the prior discussed scenario of computer system malfunction, such validation must be alert for seemingly insignificant changes that can create major errors in traditional forensic processes. Furthermore, the validation of AI/ML based software is an important and complex undertaking that must be performed by an independent entity or consortium. This level of control helps improve the consistency and quality of results from forensic laboratory processes. | |||
====Validation and change control scenario==== | |||
In this scenario, image that a forensic laboratory routinely validates and tests equipment, and maintains strict change control procedures for computers used to process evidence. Every aspect of the systems gets covered, including the specific hardware, firmware, and software versions. Validation of the forensic processes gets performed on the specific systems, and any issues are recognized and dealt with before causing further problems. | |||
===Forensic-by-design automation=== | |||
Forensic laboratories are developing new automated systems, including those with AI/ML capabilities, to analyze data and to gain understanding of crime in ways that were previously not feasible.<ref name="MargagliottiMachine19" /><ref name="CaseyTheKodak18">{{cite journal |title=The Kodak Syndrome: Risks and Opportunities Created by Decentralization of Forensic Capabilities |journal=Journal of Forensic Sciences |author=Casey, E.; Ribaux, O.; Roux, C. |volume=64 |issue=1 |pages=127–36 |year=2019 |doi=10.1111/1556-4029.13849}}</ref> | |||
====Forensic artificial intelligence scenario==== | |||
In this scenario, imagine that electronic portable devices, based on near-infrared spectroscopy and supported by machine learning, have been developed to test drugs rapidly. These devices could be useful for producing a full profile of the substance tested in the field and transfer the data to a computerized repository in the laboratory for further analysis.<ref name="CoppeyProvid20">{{cite journal |title=Providing illicit drugs results in five seconds using ultra-portable NIR technology: An opportunity for forensic laboratories to cope with the trend toward the decentralization of forensic capabilities |journal=Forensic Science International |author=Coppey, F.; Bécue, A.; Sacré, P.-Y. et al. |volume=317 |at=110498 |year=2020 |doi=10.1016/j.forsciint.2020.110498}}</ref> Such a repository could be useful for tracking drug trends in a region, and quickly detecting a problem such as an [[epidemic]]. | |||
The value of forensic laboratories can be extended to more proactive intelligence-led approaches based on knowledge extracted from repetitions found in crime.<ref name="CaseyTheKodak18" /> To manage the associated risks, systems supporting such intelligence-based solutions should be forensic-by-design, abiding by forensic principles and human rights, including privacy and nondiscrimination. Forensic-by-design includes traceability, encryption, and impossibility even for system administrators to access private information. | |||
==Digital transformation risk management== | |||
This section describes a series of recommendations (Table 1) for managing risks of digital transformation of forensic laboratories. Forensic laboratories need to prepare for matters such as lost evidence, being audited or investigated, and responding to civil lawsuits. In the digital forensic domain, the practice of forensic preparedness has been developed to manage risks associated with computer use and misuse. The practice of forensic preparedness involves specification of a policy that lays down a consistent approach, detailed planning against typical (and actual) audit or investigative scenarios that an organization faces, identification of (internal or external) resources that can be deployed as part of those plans, identification of where and how the associated digital evidence can be gathered that will support investigation, and a process of [[Continual improvement process|continuous improvement]] that learns from experience.<ref name="CESGoodPrac15">{{cite journal |url=https://vdocuments.mx/download/good-practice-guide-forensic-readiness-ncsc-site-18aa-forensic-readiness |title=Forensic Readiness |journal=Good Practice Guide |author=CESG |issue=1.2 |year=2015}}</ref> | |||
{| | |||
| STYLE="vertical-align:top;"| | |||
{| class="wikitable" border="1" cellpadding="5" cellspacing="0" width="60%" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;" colspan="3"|'''Table 1.''' Road-map for digital transformation risk management | |||
|- | |||
! style="background-color:#dddddd; padding-left:10px; padding-right:10px;"|Risk | |||
! style="background-color:#dddddd; padding-left:10px; padding-right:10px;"|Recommendation | |||
! style="background-color:#dddddd; padding-left:10px; padding-right:10px;"|Associated subsection (below) | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Not knowing what data exist | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Develop a digital evidence map documenting where needed data, logs, and provenance details are located and how they will be preserved in a forensic manner. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Curated digital information" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Not having a plan | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Institute policies and procedures that govern the roles, responsibilities, and expected actions during an inquiry. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Established processes and procedures" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Missing data and metadata | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Implement an automated digital forensic preservation process of primary data sources. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Data integrity" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Lack of traceability | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Maintain and forensically preserve detailed electronic audit logs of all computer system usage and database transactions. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Strategic audit logging" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Lack of data integrity | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Tamperproof the digitalized chain of custody ledger to support authentication of data files and audit logs. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Data authentication" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Lack of practice | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Use audit logs and digitalized chain of custody records for routine purposes to ensure that the logs are monitored and used regularly. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Regular use or review of data and processes" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Insufficient validation | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Validate computer-reliant forensic processes whenever there are changes to hardware or software configurations. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Test and validation" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Black-box automation | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Evaluate automated systems at three levels: performance, understandability, and scientific interpretation. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Effective use of automation" | |||
|- | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Lack of digital forensic support | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|Engage digital forensic expertise in preparation for problems, and to assist with dealing with problems that arise in a forensic laboratory. | |||
| style="background-color:white; padding-left:10px; padding-right:10px;"|"Role of digital forensic expertise" | |||
|- | |||
|} | |||
|} | |||
Revision as of 23:14, 29 March 2021
| Full article title | Digital transformation risk management in forensic science laboratories |
|---|---|
| Journal | Forensic Science International |
| Author(s) | Casey, Eoghan; Souvignet, Thomas R. |
| Author affiliation(s) | University of Lausanne |
| Primary contact | Email: thomas dot souvignet at unil dot ch |
| Year published | 2020 |
| Volume and issue | 316 |
| Article # | 110486 |
| DOI | 10.1016/j.forsciint.2020.110486 |
| ISSN | 0379-0738 |
| Distribution license | Creative Commons Attribution 4.0 International |
| Website | https://www.sciencedirect.com/science/article/pii/S0379073820303480 |
| Download | https://www.sciencedirect.com/science/article/pii/S0379073820303480/pdfft (PDF) |
|
|
This article should be considered a work in progress and incomplete. Consider this article incomplete until this notice is removed. |
Abstract
Technological advances are changing how forensic laboratories operate in all forensic disciplines, not only digital. Computers support workflow management and enable evidence analysis (physical and digital), while new technology enables previously unavailable forensic capabilities. Used properly, the integration of digital systems supports greater efficiency and reproducibility, and drives digital transformation of forensic laboratories. However, without the necessary preparations, these digital transformations can undermine the core principles and processes of forensic laboratories. Forensic preparedness concentrating on digital data reduces the cost and operational disruption of responding to various kinds of problems, including misplaced exhibits, allegations of employee misconduct, disclosure requirements, and information security breaches.
This work gives pertinent examples of problems and risks involving technology that have occurred in forensic laboratories, along with opportunities and risk mitigation strategies, based on the authors’ experiences. It also presents recommendations to help forensic laboratories prepare for and manage these risks, to use technology effectively, and ultimately strengthen forensic science. The importance of involving digital forensic expertise in risk management of digital transformations in laboratories is emphasized. Forensic laboratories that do not adopt forensic digital preparedness will produce results based on digital data and processes that cannot be verified independently, leaving them vulnerable to challenge. The recommendations in this work could enhance international standards such as ISO/IEC 17025, which are used to assess and accredit laboratories.
Keywords: forensic science, digital transformations, forensic laboratories, forensic preparedness, forensic digital preparedness, risk management, ISO/IEC 17025
Introduction
Forensic science laboratories are becoming more reliant on computers and data for both administrative and analytical operations. These technological advances create new opportunities and risks for all forensic disciplines, not only to digital evidence.[1] With proper preparation and management, forensic laboratories can employ technology effectively to improve performance and quality, while mitigating the associated risks. However, many forensic laboratories do not understand the subtlety and expertise required to manage risks of digital transformation, inadvisedly treating it as simply a technical component of existing quality management processes. Forensic laboratories that fail to realize the need for forensic digital preparedness to actively manage risks associated with digital transformations are vulnerable to significant expense, disruption, and liability when problems arise.
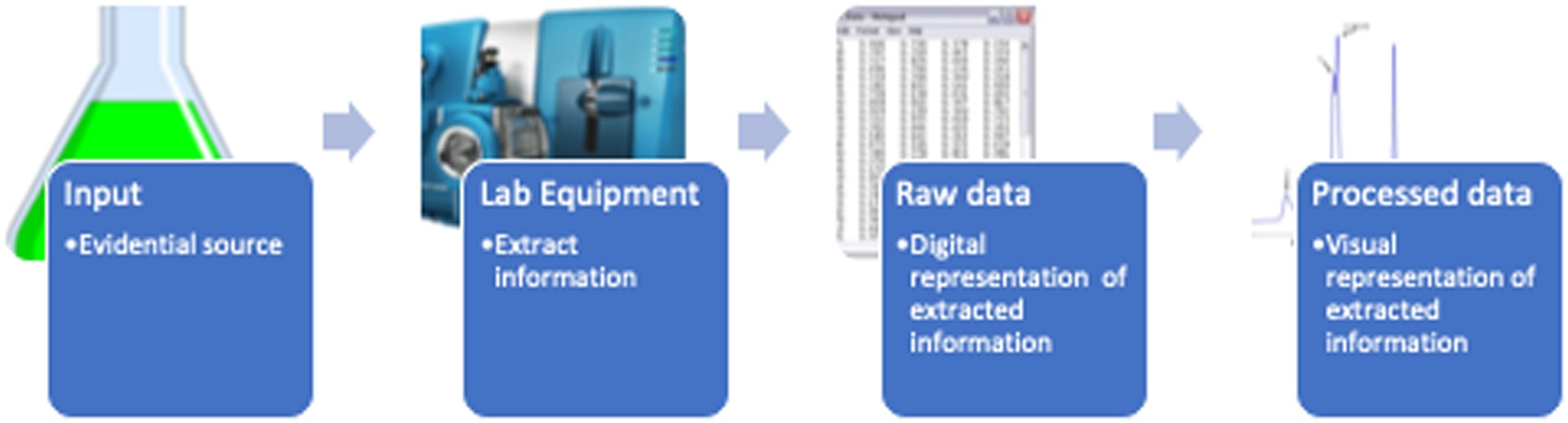
Forensic laboratories rely on technology for much more than communication and routine business functions. Sophisticated equipment for processing chemical and biological materials are operated using computers and save results in digital form. Mass spectrometers, DNA analysis systems, and other laboratory equipment save their results in raw data files. Digital evidence is processed using specialized hardware and software, although not all forensic laboratories have integrated this new discipline. Forensic laboratories are using computerized case management systems for tracking treatment of all evidential exhibits and forensic results. Automated systems with artificial intelligence (AI) are being used to support forensic analysis. In reality, digital transformations—the use of digital technology to make existing processes more efficient and effective, and to develop new solutions to emerging problems—are well underway, and forensic laboratories require a robust strategy to manage the associated risks and realize the opportunities.
This increased dependence on digital technology creates risks and opportunities for forensic laboratories. Potential pitfalls include loss of data needed to perform forensic analysis, errors in analysis of physical traces (e.g., DNA, fingerprint, face) caused by computer hardware or software, ability to tamper with raw data files generated by laboratory equipment, and incorrect information input into laboratory information management systems (LIMS). Possible benefits are traceability and integrity of traces, reliability and reproducibility of results from information extracted from traces and stored as raw data, and use of AI to support forensic analysis.
Lessons can be learned from the digital forensic domain, including forensic digital preparedness and accreditation challenges. Primary challenges encountered by digital forensic laboratories adopting quality standards include[2]:
- Inaccurate or insufficient information in technical records, including chain of custody, and no mechanism to detect subsequent changes to records.
- Problems with the security of information technology systems and the backup processes of data.
- Missing or insufficiently detailed procedures for treating digital data, and personnel not following documented procedures consistently.
- Lack of robust quality checking mechanisms, and issues with validation of methods.
This paper presents risks and opportunities associated with digital transformation of forensic laboratories, providing examples based on the authors’ experiences. Examples have been anonymized, as the intention is to illustrate general lessons learned rather than critique specific laboratories. This work then presents forensic digital preparedness, a set of recommendations to help laboratories navigate risks associated with digital transformations, including mishandled exhibits, allegations of employee misconduct, and disclosure requirements. The role of digital forensic capabilities and expertise in risk management of digital transformations in laboratories is discussed. This work culminates with broader implications for international standards such as ISO/IEC 17025, which are used to assess and accredit laboratories.
Risks and remedies
Many processes in forensic laboratories have become digitalized through the increased use of information management systems and software running analysis instruments. While these systems serve crucial functions in modern forensic laboratories, thet also have associated risks that must be managed.
Data retention
The computer systems used to store instruments' generated data files (raw and processed) can encounter problems that lead to loss of information.
Data loss scenario
In this scenario, Reust et al.[3] presented a case study concerning a forensic laboratory that performed DNA analysis of a crime scene sample relevant to a multiple homicide and death penalty case, but did not retain a copy of the raw data files. To comply with a court order to provide the defense with original raw data, it was necessary to perform costly forensic data recovery on the computer used to perform the original processing of DNA. The authors developed a customized software utility to automatically search the computer hard drive for all fragments of the relevant raw data and reconstruct the original files. The resulting files were tested and validated with DNA analysis software.
As seen with Reust et al., original data files thought to be lost can, under certain circumstances, be recovered from hard disks using digital forensic methods, which can be costly and time-consuming. Even when digital data is retained, it is malleable and subject to undetected alterations of content or metadata. Lack of proper data retention processes makes it more difficult, sometimes impossible, to recover original data files and verify their integrity.
Generally, normal backup processes do not have the fidelity of digital forensic preservation mechanisms. To manage the risks of data loss and undetected alterations, traditional data retention practices in forensic laboratories can be updated to employ digital forensic preservation methods. Specifically, as part of routine data retention processes, digital forensic preservation of original data (raw and processed) and associated metadata (filesystem timestamps) allows the integrity of data to be verified more easily when there is a problem or inquiry. For instance, original files and associated metadata can be forensically preserved using the Advanced Forensic Format (AFF4), which is open-source and cross-platform. The following command and resulting output demonstrate how this method can be implemented on any type of computer system with a single command that can be part of a routine or automated process to forensically preserve all raw data files in a specified directory on a laboratory computer, while generating a unique identifier for the digital evidence container for evidence management purposes[4][5]:
% aff4.py -cr s1-001-10April2020.aff4 RAWdata/s1-001
Creating AFF4Container: file://s1-001-10April2020.aff4
<aff4://c293153c-a317-4927-b1eb-6e3a5008ad0f>
Adding: RAWdata
Adding: RAWdata/s1-001/s1-001-sequence.sld
Adding: RAWdata/s1-001/s1-001-processed.pdf
Adding: RAWdata/s1-001/s1-001-ref.params
Adding: RAWdata/s1-001/s1-001.RAW
This digital forensic preservation process captures file system metadata and automatically computes MD5 and SHA1 cryptographic hash values of the acquired data for integrity verification purposes as the following excerpt shows:
% aff4.py -m s1-000-10April2020.aff4
... EDITED FOR BREVITY...
<aff4://c293153c-a317-4927-b1eb-6e3a5008ad0f/RAWdata/s1-001/s1-000.RAW>
a aff4:FileImage,
aff4:Image,
aff4:ImageStream;
aff4:birthTime “2020-04-10T22:41:03.949269+02:00”^◯sd:dateTime;
aff4:hash “1d2f7ff1ea563ceb6d2da0e168e90587”^âff4:MD5,
“427bc17e608fc493f0e2b3fed8fa55b36862ac31”^âff4:SHA1;
aff4:lastAccessed “2020-04-10T22:41:08.708498+02:00”^◯sd:dateTime;
aff4:lastWritten “2020-04-10T22:41:05.290019+02:00”^◯sd:dateTime;
aff4:originalFileName “RAWdata/s1-001/s1-000.RAW”^◯sd:string;
aff4:recordChanged “2020-04-10T22:41:07.694584+02:00”^◯sd:dateTime;
aff4:size 276196936.
These hash values are commonly used in digital forensic tools to enable future verification that the acquired data have not been altered since they were forensically preserved. The preserved metadata can also be useful for assessing the authenticity of the acquired data, including the original file name, size and creation timestamp.
Additionally, AFF4 assigns a unique identifier to the acquired data to support evidence management and provenance tracking.
Evidence integrity
The data files generated by laboratory equipment and stored on computers can be altered afterwards accidentally or intentionally.
Data alteration scenario
In this scenario, imagine data files stored on laboratory computers have been altered to conceal specific information in test results. Some alterations were detectable within the digital file, while others were not detected using available verification software. As a result, it was difficult to determine the full scope and specific impact of the alterations.
The motivation for editing the data files (raw and processed) might be to cover up mistakes, conceal unfavorable results (corruption), facilitate prosecution (bias), or inflate laboratory metrics (performance)[6] Forensic laboratory personnel might modify data to remove traces of contamination they considered to be insignificant, such as traces of investigators operating an evidential smartphone after the device was seized. Depending on the type of data and the method of modification, it might be possible to detect the alteration. However, some alterations may be undetectable using existing verification tools, making it more difficult to determine that modifications were made.
Normal backup processes, and even digital forensic preservation such as described in the previous section using AFF4, are not tamperproof because data can be forged to replace retained data, and a computer system can be backdated to make it seem to have occurred sometime in the past. Lack of a tamperproof chain of custody of primary data sources in a forensic laboratory makes it more difficult, sometimes impossible, to authenticate original data files that form the basis of forensic findings and reported results.
To manage the risks of inadvertent alteration and intentional tampering, traditional provenance tracking practices in forensic laboratories must be updated to employ digitalized chain of custody ledger solutions.[7][8] These digitalized chain of custody mechanisms can be implemented in a way that is tamperproof and independently verifiable.
Data traceability
Forensic laboratories are increasingly using a LIMS to record information about the full lifecycle of evidence in a forensic laboratory, including submission data, chain of custody, and results. A typical LIMS uses databases to store and organize information about each item of evidence at different stages of its treatment in the laboratory.
A LIMS is invaluable for keeping track of the growing amount of evidence and associated processes and results in forensic laboratories. As a result, such systems are considered essential for laboratory accreditation under standards such as ISO/IEC 17025. However, these systems can have weaknesses, including user-based data entry errors, programming bugs, and system administrator bypass of access controls.
LIMS weaknesses scenario
In this scenario, imagine that the results of drug tests have been routinely recorded in a LIMS, and normal users of the system can only create new records and view existing records. However, a system administrator was able to alter records using his higher level access, bypassing the security control mechanisms of a LIMS. As such, the LIMS maintained an audit log of all normal user activities, but did not log administrator-level actions.
To manage these risks of undetected or unattributed alterations to LIMS data, it is necessary to require unique user accounts for all actions and to maintain detailed electronic audit logs. These audit logs must include successful actions, not only failed or blocked actions. Specifically, all transactions must be recorded (additions, alterations, deletions), and all computer system usage, such as logons and executed commands. In particular, system administrator accounts should be strictly protected (e.g., via two-factor authentication) and monitored (e.g., via sudo logging and process accounting). All audit logs must be preserved in a forensically sound manner in anticipation of their use as digital evidence in a legal matter. Applying digital forensic preservation and digitalized chain of custody on logs generated by a LIMS and other supporting computer systems can be an efficient way to enhance LIMS traceability.
Computer system malfunction
Forensic laboratories increasingly depend on computers to operate equipment for extracting information from biological and chemical samples (Figure 1).
|
The computer systems used to operate laboratory equipment can malfunction, introducing errors in forensic analysis.
Hardware issues scenario
In this scenario, imagine, unbeknownst to administrators, a few DNA analysis systems in a forensic laboratory are operated by computers with slightly different hardware than the standard configuration. This seemingly minor difference inevitably caused read errors, which resulted in erroneous reference data being accessed on the DNA analysis systems. As a result, incorrect reference data were used in some cases, and the forensic analysis had to be repeated. This demonstrates that a seemingly unrelated problem with computer used to operate equipment for performing laboratory processes can cause incorrect results.
This exemplifies how seemingly minor changes to underlying computer systems can interfere with traditional forensic processes. Although validation of computer systems can be covered under existing laboratory management processes, the subtleties of computer hardware and software configurations and interactions must not be underestimated.
Automation complexity and pitfalls
In forensic contexts, use of automated systems, including those with AI and machine learning (ML), support analysis performed by human specialists who interpret the results. Although such automation can help maintain consistency and increase efficiency in forensic analysis, there are several major limitations that must be guarded against. Automated systems can have bugs that produce incorrect results, which can have serious consequences in a forensic context.[9] Additionally, automated AI/ML systems can introduce bias due to poorly selected training datasets, and can lead to misinterpretations when the results are not fully understood.[10] When automated AI/ML systems are used to support investigation and forensic analysis, such as comparison of faces in digital video or photographs, algorithmic false positives can lead to incorrect results.
Reliability and human rights concerns scenario
In this scenario, an independent study of six facial recognition technology test deployments performed by the London Metropolitan Police Service (MPS) found a high number of false positives. In total, only eight out of 46 automatically generated potential face recognition “matches” that were considered and evaluated by a human were deemed to be correct. The eight verified correct matches were determined by some form of confirmation such as through a street-based identity check.[11] The study paid particular attention to the risks of such technology interfering with fundamental human rights, including privacy violations and discrimination due to algorithmic bias relating to sex, race, or ethnicity.
This study highlights the fact that any automated system can have some false positives and false negatives, which demands that human analysts are in the loop to manage the risks of something important being overlooked or misinterpreted. Good practice here can also help deal with the risk of contextual bias. An automated system supporting forensic analysis should offer sequential unmasking capabilities.[12]
Ultimately, automated systems supporting forensic analysis should integrate forensic requirements, risk management, and privacy, i.e., forensic-by-design. If a system is forensic-by-design, forensic preparedness principles and practices have been integrated into the system engineering lifecycle, including risk management, incident handling, forensic principles, and legal compliance.[13] However, such forensic-by-design is not common practice at the moment, and there are growing concerns about the unreliability and invasiveness of such technologies for criminal investigation purposes. Some cities in California are strictly controlling the acquisition and utilization of "any software, electronic device, system utilizing an electronic device, or similar device used, designed, or primarily intended to collect, retain, process, or share audio, electronic, visual, location, thermal, biometric, olfactory or similar information specifically associated with, or capable of being associated with, any individual or group."[14]
Forensic laboratories must be prepared to address concerns about reliability, privacy, and discrimination associated with use of technology for processing data, particularly AI/ML systems for data analysis.
Digital reinforcement of forensic science principles
Core principles and processes in forensic laboratories can be bolstered using technology while increasing the efficiency and quality of services. These core principles include authenticity and integrity; reliability and reproducibility; and quality and efficiency. In addition, intelligent application of digital technology can create new opportunities to deal with crime in digitalized society.
Authenticity and integrity
Digital transformation of forensic laboratories can enhance the traceability of traces. Existing computerized systems for processing physical and digital evidence typically provide a digital audit trail and its treatment throughout its lifecycle in the forensic laboratory. Alterations to data files (raw and processed) might be detectable using the digital traces that are created routinely during the processing of exhibits in a forensic laboratory. In some situations, to authenticate data files and associated results, it is necessary to perform contextual analysis, including digital forensic analysis of the original data and metadata.
Contextual reconstruction scenario
In this scenario, questions have arisen about the results of some samples processed by a laboratory. In order to assess the reported results, the raw data was recovered from analysis systems along with processed results. The information from these files was compared with details recorded in the LIMS, and discrepancies were found. However, audit logs in the LIMS were found that corresponded with the original data. Timestamps of the original data files and the LIMS were also examined to determine contemporaneous activities versus later changes.
As this scenario highlights, it is advisable not to leave evidence authentication to chance. With properly protected audit trail and data file integrity mechanisms (preferably automated), a digitalized chain of custody can be maintained from evidence intake to evidence return or archiving, providing valuable insights into laboratory operations and helping protect against undetected mistakes and forensic fraud. Some forensic laboratories have adopted bar code scanning and RFID labels to mark and track exhibits throughout their lifecycle. Some forensic laboratories use secure storage to retain raw data files. Some laboratories are developing enhanced methods for maintaining provenance information using blockchain-based systems.[7][8]
With such automated provenance tracking mechanisms in place, every deliverable that a forensic laboratory produces could include the associated electronic chain of custody details as an appendix to demonstrate proper handling. Providing this provenance information in a standardized format such as CASE enables receiving organizations to integrate the information into their information management systems and detect potential inconsistencies more easily, and even automatically.
Reliability and reproducibility
Forensic science practices demand that the data, methods, tools, and analysis are described in sufficient detail that they can be carried out again with the same results.
Digital transformations can support reproducibility of processing by documenting all phases of the evidence lifecycle in the forensic laboratory, as well as reproducibility of analysis by providing others with original data to perform independent analysis. Some software developers also provide a standalone application for viewing the results of forensic processes, enabling others to verify forensic analysis without requiring them to purchase licenses for the specific software and/or version.
Reproducibility of forensic analysis scenario
In this scenario, multiple parties need to perform an in-depth review of the results produced by a forensic laboratory, as part of an investigation involving various computers and mobile devices. To save cost and time, the forensic laboratory provided the multiple parties with a complete package of data and viewing software necessary to perform in-depth review. Using this approach, all parties could assess the reliability of the evidence and results without having to purchase specialized equipment and software, or to run time consuming data processing operations that had already been performed by the laboratory.
This scenarion shows that expanding decentralisation of forensic capabilities is driving the need for data and analysis results to be transferred securely between systems and organizations that is fully traceable, if not completely repeatable. This trend raises the importance of international standards for harmonization of forensic methods and data formats.
Quality and efficiency
Technological advances enable forensic laboratories to process evidence more quickly while maintaining quality. Forensic laboratories can manage the systems that they rely on for processing evidence in order to standardize the processing and output. The National Institute of Standards and Technology (NIST) Computer Forensic Tool Testing (CFTT) program publishes open access test reports for software commonly used in digital forensic laboratories, detailing both capabilities and limitations. The European Network of Forensic Science Institutes (ENFSI) and the US DoD Cyber Crime Center (DC3) also perform tool validation and testing, and provide the results to law enforcement agencies. Similar validation and testing should be applied to computers and software used to operate traditional forensic equipment. As with the prior discussed scenario of computer system malfunction, such validation must be alert for seemingly insignificant changes that can create major errors in traditional forensic processes. Furthermore, the validation of AI/ML based software is an important and complex undertaking that must be performed by an independent entity or consortium. This level of control helps improve the consistency and quality of results from forensic laboratory processes.
Validation and change control scenario
In this scenario, image that a forensic laboratory routinely validates and tests equipment, and maintains strict change control procedures for computers used to process evidence. Every aspect of the systems gets covered, including the specific hardware, firmware, and software versions. Validation of the forensic processes gets performed on the specific systems, and any issues are recognized and dealt with before causing further problems.
Forensic-by-design automation
Forensic laboratories are developing new automated systems, including those with AI/ML capabilities, to analyze data and to gain understanding of crime in ways that were previously not feasible.[10][15]
Forensic artificial intelligence scenario
In this scenario, imagine that electronic portable devices, based on near-infrared spectroscopy and supported by machine learning, have been developed to test drugs rapidly. These devices could be useful for producing a full profile of the substance tested in the field and transfer the data to a computerized repository in the laboratory for further analysis.[16] Such a repository could be useful for tracking drug trends in a region, and quickly detecting a problem such as an epidemic.
The value of forensic laboratories can be extended to more proactive intelligence-led approaches based on knowledge extracted from repetitions found in crime.[15] To manage the associated risks, systems supporting such intelligence-based solutions should be forensic-by-design, abiding by forensic principles and human rights, including privacy and nondiscrimination. Forensic-by-design includes traceability, encryption, and impossibility even for system administrators to access private information.
Digital transformation risk management
This section describes a series of recommendations (Table 1) for managing risks of digital transformation of forensic laboratories. Forensic laboratories need to prepare for matters such as lost evidence, being audited or investigated, and responding to civil lawsuits. In the digital forensic domain, the practice of forensic preparedness has been developed to manage risks associated with computer use and misuse. The practice of forensic preparedness involves specification of a policy that lays down a consistent approach, detailed planning against typical (and actual) audit or investigative scenarios that an organization faces, identification of (internal or external) resources that can be deployed as part of those plans, identification of where and how the associated digital evidence can be gathered that will support investigation, and a process of continuous improvement that learns from experience.[17]
| |||||||||||||||||||||||||||||||||
References
- ↑ Pollitt, M.; Casey, E.; Jaquet-Chiffelle, D.-O. et al. (February 2019). "A Framework for Harmonizing Forensic Science Practices and Digital/Multimedia Evidence" (PDF). OSAC. https://www.nist.gov/system/files/documents/2018/01/10/osac_ts_0002.pdf.
- ↑ Tully, G.; Cohen, N.; Compton, D. et al. (2020). "Quality standards for digital forensics: Learning from experience in England & Wales". Forensic Science International: Digital Investigation 32: 200905. doi:10.1016/j.fsidi.2020.200905.
- ↑ Reust, J.; Sommers, R.; Friedberg, S. et al. (2008). "Identification and Reconstruction of Deleted, Fragmented DNA Digital Files". Proceedings of the American Academy of Forensic Sciences 14: 187–88. Archived from the original on 29 April 2016. https://web.archive.org/web/20160429004454/https://www.aafs.org/wp-content/uploads/ProceedingsWashingtonDC2008.pdf.
- ↑ Cohen, M.; Garfinkel, S.; Schatz, B. (2009). "Extending the advanced forensic format to accommodate multiple data sources, logical evidence, arbitrary information and forensic workflow". Digital Investigation 6 (Supplement 1): S57–S68. doi:10.1016/j.diin.2009.06.010.
- ↑ Schatz, B.L. (2015). "Wirespeed: Extending the AFF4 forensic container format for scalable acquisition and live analysis". Digital Investigation 14 (Supplement 1): S45–54. doi:10.1016/j.diin.2015.05.016.
- ↑ Bidgood, J. (18 April 2017). "Chemist’s Misconduct Is Likely to Void 20,000 Massachusetts Drug Cases". The New York Times. Archived from the original on 19 April 2017. https://web.archive.org/web/20170419100845/https://www.nytimes.com/2017/04/18/us/chemist-drug-cases-dismissal.html.
- ↑ 7.0 7.1 Burri, X.; Casey, E.; Bollé, T. et al. (2020). "Chronological independently verifiable electronic chain of custody ledger using blockchain technology". Forensic Science International: Digital Investigation 33: 300976. doi:10.1016/j.fsidi.2020.300976.
- ↑ 8.0 8.1 Jaquet-Chiffelle, D.-O.; Casey, E.; Bourquenoud, J. (2020). "Tamperproof timestamped provenance ledger using blockchain technology". Forensic Science International: Digital Investigation 33: 300977. doi:10.1016/j.fsidi.2020.300977.
- ↑ Murray, D. (20 March 2015). "Queensland authorities confirm ‘miscode’ affects DNA evidence in criminal cases". The Courier Mail. https://www.couriermail.com.au/news/queensland/queensland-authorities-confirm-miscode-affects-dna-evidence-in-criminal-cases/news-story/833c580d3f1c59039efd1a2ef55af92b.
- ↑ 10.0 10.1 Margagliotti, G.; Bollé, T. (2019). "Machine learning & forensic science". Forensic Science International 298: 138–39. doi:10.1016/j.forsciint.2019.02.045.
- ↑ Fussey, P.; Murray, D. (2019). "Independent Report on the London Metropolitan Police Service’s Trial of Live Facial Recognition Technology". University of Essex Human Rights Centre. http://repository.essex.ac.uk/24946/.
- ↑ Koppl, R. (2019). "Strategic choice in linear sequential unmasking". Science & Justice 59 (2): 166-171. doi:10.1016/j.scijus.2018.10.010.
- ↑ Rahman, N.H.A.; Glisson, W.B.; Yang, Y. et al. (2016). "Forensic-by-Design Framework for Cyber-Physical Cloud Systems". IEEE Cloud Computing 3 (1): 50–59. doi:10.1109/MCC.2016.5.
- ↑ "Administrative Code - Acquisition of Surveillance Technology, Ordinance No. 107-19" (PDF). County of San Francisco. 21 May 2019. https://sfbos.org/sites/default/files/o0107-19.pdf.
- ↑ 15.0 15.1 Casey, E.; Ribaux, O.; Roux, C. (2019). "The Kodak Syndrome: Risks and Opportunities Created by Decentralization of Forensic Capabilities". Journal of Forensic Sciences 64 (1): 127–36. doi:10.1111/1556-4029.13849.
- ↑ Coppey, F.; Bécue, A.; Sacré, P.-Y. et al. (2020). "Providing illicit drugs results in five seconds using ultra-portable NIR technology: An opportunity for forensic laboratories to cope with the trend toward the decentralization of forensic capabilities". Forensic Science International 317: 110498. doi:10.1016/j.forsciint.2020.110498.
- ↑ CESG (2015). "Forensic Readiness". Good Practice Guide (1.2). https://vdocuments.mx/download/good-practice-guide-forensic-readiness-ncsc-site-18aa-forensic-readiness.
Notes
This presentation is faithful to the original, with only a few minor changes to presentation. In some cases important information was missing from the references, and that information was added.