Journal:Interoperability challenges in the cybersecurity information sharing ecosystem
| Full article title | Interoperability challenges in the cybersecurity information sharing ecosystem |
|---|---|
| Journal | Computers |
| Author(s) | Rantos, Konstantinos; Spyros, Arnolnt; Papanikolaou, Alexandros; Kritsas, Antonios; Ilioudis, Christos; Katos, Vasilios |
| Author affiliation(s) | International Hellenic University, Innovative Secure Technologies, Bournemouth University |
| Primary contact | Email: krantos at cs dot ihu dot gr |
| Year published | 2020 |
| Volume and issue | 9(1) |
| Article # | 18 |
| DOI | 10.3390/computers9010018 |
| ISSN | 2073-431X |
| Distribution license | Creative Commons Attribution 4.0 International |
| Website | https://www.mdpi.com/2073-431X/9/1/18/htm |
| Download | https://www.mdpi.com/2073-431X/9/1/18/pdf (PDF) |
Abstract
Threat intelligence helps businesses and organizations make the right decisions in their fight against cyber threats, and strategically design their digital defenses for an optimized and up-to-date security situation. Combined with advanced security analysis, threat intelligence helps reduce the time between the detection of an attack and its containment. This is achieved by continuously providing information, accompanied by data, on existing and emerging cyber threats and vulnerabilities affecting corporate networks. This paper addresses challenges that organizations are bound to face when they decide to invest in effective and interoperable cybersecurity information sharing, and it categorizes them in a layered model. Based on this, it provides an evaluation of existing sources that share cybersecurity information. The aim of this research is to help organizations improve their cyber threat information exchange capabilities, to enhance their security posture and be more prepared against emerging threats.
Keywords: cyber threat information, cyber threat intelligence, interoperability, cybersecurity, evaluation
Introduction
Information has undoubtedly become one of the most valuable assets for organizations, whose dependence on it is constantly rising. At the same time, the frequency and ferocity of cyberattacks is also increasing, posing a great threat to business environments. According to a study conducted jointly by Ponemon Institute and Accenture, the average cost of cybercrime to organizations in 2018 rose to $13 million.[1] Moreover, 79% of chief information security officers (CISOs) in the banking sector believe that cybercriminals have become more sophisticated.[2]
In this constant battle of cybersecurity, organizations must remain cognizant of emerging and evolving threats and defend themselves against a wide range of adversaries with various levels of motivations, capabilities, and access to resources. These adversaries typically range from amateur hackers to well-organized and highly capable teams that have direct access to vulnerabilities and exploits, and therefore become advanced, and sometimes persistent, threats to organizations. The impact of such sophisticated, dynamic, and automated cyberattacks can be devastating.
Various businesses and organizations have recognized the need of being able to share cyber threat information (CTI) in a timely and reliable manner to enhance their ability to identify any malicious activity or sources and mitigate attacks in a timely manner, prior to damaging their assets. The National Institute of Standards and Technology (NIST) defines CTI as "any information that can help an organization identify, assess, monitor, and respond to cyber threats."[3] In a survey conducted by the SANS institute regarding the evolution of cyber threat information, 72% of survey respondents mentioned that in 2018 they had produced or consumed such information for their network defense.[4] The respective percentage for 2017 was 60%.[4] This demonstrates that information sharing is increasingly becoming part of an organization's strategy, and the number of them that join the sharing community is rising. The types of information that can be produced and shared among communities include, among others, security appliance log entries and alerts, measurable and observable actions, security bulletins and advisories, identified vulnerabilities, news, reports, and intelligent information.
The number of CTI sources is therefore increasing, as do cyber threat intelligence platforms capable of consuming information from threat intelligence feeds, analyzing, evaluating, and classifying it prior to sharing threat information with the community. Threat intelligence, according to Tounsi and Rais[5], means evidence-based knowledge representing threats that can inform decision-making. Cyber threat information and intelligence (CTII) facilitate situational awareness of the threat landscape, a deeper understanding of threat actors and their tactics, techniques, and procedures (TTPs), and greater agility to defend against evolving threats.
Nowadays, organizations have the ability to participate in such threat-sharing communities or intelligence groups, and analyze and evaluate CTII via their security operations team. Depending on the types of security appliances they are using, they can incorporate CTII into their security solutions, including measures such as unified threat management (UTM), intrusion detection/prevention systems (IDS/IPS), and security information and event mnagement (SIEM). IT security vendors and service providers also collect such information from their clients worldwide, analyze it, and feed it back to the deployed security appliances, thus gaining from the experience of their community. Analysis and evaluation of such information is considered essential, as sometimes the information that is shared is not properly filtered or checked.
Using unreliable sources poses risks to organizations, as the information may not be accurate or complete. To confront this undesired situation, organizations go beyond closed groups and use multiple sources instead. As such, CTII sharing takes place among multiple actors, such as government agencies and organizations, private sector organizations, and industry-based focus groups. One of the most challenging issues in this process is achieving consensus regarding how this information should be shared among interested parties and the threat intelligence community. This requires having a common understanding on what information is shared, how it is shared, and whether sharing of such information is legal.
This paper addresses the interoperability challenges that businesses and organizations face when adopting specific sharing solutions. These challenges mainly stem from the adoption of multiple technical standards, strategies, and policies among stakeholders, together with legal restrictions concerning information sharing. The aim of this work is to highlight points that impede the wide adoption of cybersecurity information sharing and the much-needed automation of the sharing process.[4] Security analysts would benefit from such automation, as they could devote more time on analyzing collected interoperable data, as opposed to devoting their efforts on the collection process itself. Interoperability is also a means to widen the CTII sharing spectrum and engage more stakeholders in the exchange process, thus developing a global shield against emerging threats, with significant benefits for the community.
Background
Cybersecurity information exchange (CIE) concerns sharing CTII with third parties to help organizations enhance their security posture and protect themselves from cyber threats. The main motive is to create new knowledge or services about cyber threats, as well as to make cyber-defence systems more effective and efficient.
CTI can be sometimes directly imported to security appliances, e.g., IP addresses reported as malicious can be directly imported to firewalls and IDS/IPS, to speed up the organization’s reaction to a potential threat. This, however, may come at the cost of introducing many false positives as, after an in-depth analysis and evaluation, these IPs may prove to be non-malicious. Therefore, prior to becoming a valuable asset for the organization, cyber threat information has to be properly collected from various sources, correlated, analyzed, and evaluated to add significant value to the raw and/or unevaluated data, thus producing the so-called “cyber threat intelligence.” Analyzed information significantly reduces false positives and establishes trust on the various sources it comes from. The downside of this process is the delay introduced to information sharing, due to the time-consuming analysis of, e.g., big data as well as other techniques, like threat sandboxing, which is used for monitoring the behavior of suspicious targets.
The cooperation among organizations in the E.U. and the publication of detected security incidents are also encouraged, although there are also cases where they are obligatory, as stated in E.U. Directive 2016/1148 on the security of network and information systems.[6] Implementation guidance for meeting the requirements of that directive is provided by ETSI.[7] In this context, a computer security incident response team (CSIRT; also known as computer emergency response team or CERT) network has been established, which counts more than 400 members willing to share incidents and risk-related information (an inventory of the E.U.'s CSIRT network members is maintained by ENISA[8]). The network, however, is not restricted only to CSIRTs, but also includes commercial organizations, E.U. institutions, law enforcement agencies, private- and public-sector organizations, and national and military agencies.
Similar initiatives in the U.S. that promote the exchange of information include the U.S. Department of Homeland Security (DHS) Cyber Information Sharing and Collaboration Program (CISCP)[9] and its Automated Indicator Sharing (AIS) capability.[10]
Examples of such shareable information include the following:
- indicators of compromise (IOCs), i.e., system artifacts or observables that contain patterns, such as malicious Internet Protocol addresses (IPs) or hashes of files containing malware, which can help identify suspicious or malicious activity;
- tactics, techniques, and procedures (TTPs), i.e., (detailed) descriptions of the behavior of an actor that can assist operational activities, such as details of exploits and malware delivery mechanisms (examples include tradecrafts, i.e., behaviour used to conduct a malicious activity, infrastructure used to deliver malicious content or maintain command and control capabilities, and attackers’ intentions[11]);
- security alerts, i.e., notifications—usually human-readable—regarding security issues, such as vulnerabilities;
- threat intelligence reports, i.e., collections of threat intelligence for various topics, such as threat actors, malware, and attack techniques;
- recommended security tool configurations, regarding automated collection and processing as well as healing of identified security issues; and
- vulnerabilities, i.e., known weaknesses in software implementations or procedures, and corresponding mitigations, such as security patches (although in the information security literature, vulnerabilities are not threats, they are considered an important component in the CTII sharing ecosystem).
The U.K. National Computer Emergency Response Team CERT-UK, together with the U.K.’s Centre for the Protection of National Infrastructure, define four subtypes of threat intelligence in a whitepaper published by MWR Infosecurity.[12] A similar categorization is also adopted by ENISA.[13] Based on the two schemes, stakeholders exchange information of one of the following types:
- strategic reports providing high-level threat analyses that are consumed at board level or by other senior decision-makers;
- operational details providing information about impending attacks against an organization;
- advisories which include vulnerabilities, exploits, patches and patch statuses, or high-level tactical patterns of activity on host-, service-, network-, or internet-level tools and methodologies;
- indicators of compromise, which include IP addresses, DNS names, URLs, specific values of format-specific fields (e.g., email headers), artifacts (e.g., hashes, registries, and keys) related to malware and sequences of low-level events (e.g., syscalls and packets) linked to malicious behavior; and
- low-level activity, i.e., network flow records and full packet captures, application logs, including typical IDS alerts, samples of executable files, documents, and email messages.
Depending on the type of information that is being shared, organizations have the capability for prompt reaction, as a response to newly-emerged threats or vulnerabilities, for properly adapting their security defenses against changes in their situational awareness at a more tactical level, while making more strategic decisions on the allocation of their resources for upcoming threats.
Tounsi and Rais[5] classify and distinguish existing threat intelligence types, focusing on technical threat intelligence issues, emerging research, trends, and standards. They also explain why there is a reluctance among organizations to share threat intelligence, while also providing sharing strategies that can help overcome policy interoperability issues. Following a layered model, Burger et al.[14] propose a taxonomy to help classify existing threat-sharing standards and analyze interoperability. However, the five layers proposed by the authors do not address legal or semantic issues that are analyzed in this paper.
So far, although CTII sharing is identified in the literature as an important issue, it is treated as a problem that can be solved with the adoption of some technical standards.[3][14][15] To the best of the authors’ knowledge, no work has been published so far detailing a holistic approach to the interoperability problem of CTII sharing.
Interoperable CTII sharing
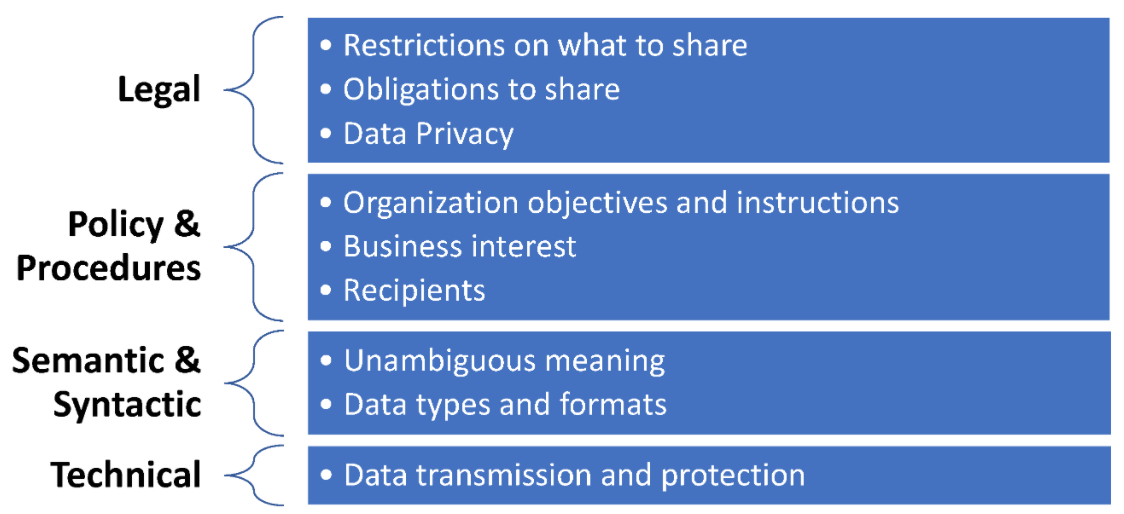
Cyber threat information and intelligence (CTII) information is generated and shared among devices and organizations that typically have well-established procedures to appropriately handle [[Information privacy|personal] and classified information found within. When CTII is about to be shared, especially with external entities, several interoperability and security issues have to be confronted. These issues can be categorized into the four layers depicted in Figure 1, further analyzed in the following sections.
|
Legal interoperability
Legal interoperability is about ensuring that the legal frameworks under which organizations operate and provide services are aligned and do not impede the sharing of CTII. Legal frameworks open up the potential for improving the collaboration among public–private organizations and may encourage or require the sharing of cyber threat information. Examples of such frameworks are the E.U.’s NIS Directive[6] and the U.S. Cybersecurity Information Sharing Act (CISA) of 2015.
Legal constraints may also prohibit or restrict the uncontrolled sharing of CTII. Examples of the latter are any personally identifiable information (PII) that may be part of the shared sightings, such as usernames of entities that have been identified as sources of malicious activity and restrictions that stem from the corresponding telecommunications privacy legal framework. One of the main legal restrictions arises from the E.U.'s General Data Protection Regulation (GDPR)[16] and relates to any PII shared with external entities without the user’s consent. CTII sharing with external entities should not impact privacy, and sharing parties must take measures to properly anonymize or pseudonymize any records of data that could otherwise be used to identify individuals.
Liability is another key factor that has to be considered when sharing information. Organizations have to take into account that they may be liable for any damage caused to stakeholders or entities that appear to be threat actors, by sharing information that may prove inaccurate or false. For instance, what would happen if an IDS/IPS falsely identified some malicious activity coming from a popular website and this was immediately reported to sharing parties?
Legal interoperability is even more important when data sharing spans multiple countries or legal domains. Therefore, restrictions imposed by each such domain must be carefully reviewed prior to information dissemination. The organization has to establish boundaries on any sharing activities so that these will not infringe on any legal restrictions.
As such, legal interoperability requires visibility control over CTII. The organization has to have the means to perform deep inspection on what is practically going to be shared to identify any information that may cross the well-established boundaries regarding information sharing, and this should be reflected to the policies and procedures adopted by the organization.
Policies and procedures for interoperability
An organization's information sharing policies and procedures are formal statements that reflect its objectives and detailed instructions to achieve these objectives respectively. They are typically part of the organization’s information security policy and have to be endorsed by the organization’s top management.
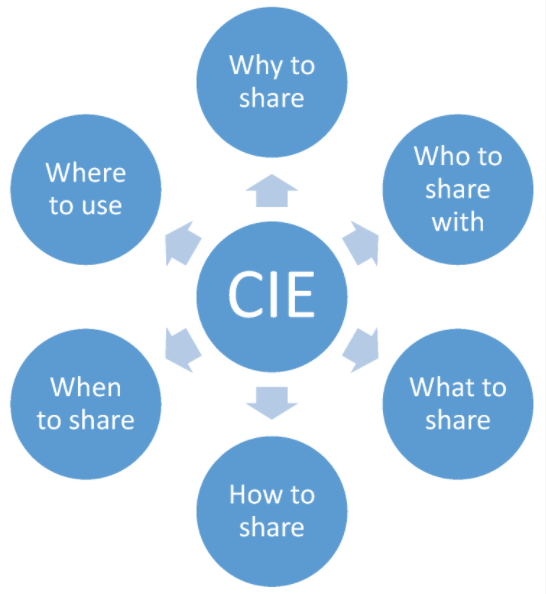
Among the issues that the organization has to consider at the policy layer when deciding to share CTII are the five "Ws" and one "H" that have to be answered prior to sharing, as depicted in Figure 2. The policy should clearly address them, while well-established procedures and appropriate robust measures will properly support them to avoid policy violations, such as the leakage of classified or sensitive information. Therefore, to ensure that the security and privacy posture of the organization is not negatively affected by the introduction of CTII sharing, the service’s risk analysis should address the threats that are associated with the exchange of CTII with third parties and the consumption of the received information. The deployed security measures that will protect CTII and ensure that this is handled only by authenticated and authorized entities will minimise the associated risks.
|
The adopted procedures should facilitate information sharing according to the organization’s strategy and policy and should not be an impediment to the accurate, fast, and secure exchange of high-quality information. Organizations’ policies may also be driven by security-related standards that address the sensitive issue of information sharing, such as the ISO 27010:2015[17], which provides guidance on managing information within sharing communities and therefore facilitates trust establishment among stakeholders. Trust establishment with stakeholders is the foundation in CTII sharing and should be mainly addressed in the context of the “Who to share it with” question. A methodology that can be used for evaluating CTII sources based on quantitative parameters is proposed by Schaberreiter et al.[18] The methodology is based on a weighted evaluation method that allows each entity to adapt it to its own needs and priorities.
In the context of formulating its policy and procedures, an organization may consider adopting a cybersecurity sharing framework for managing cyber threat information, which sets provisions for information sharing and exchange. There are several frameworks and programs adopted and supported by governments or the industry, like the U.S. Department of Homeland Security’s (DHS) Automated Indicator Sharing (AIS)[10] and Cyber Information Sharing and Collaboration Program (CISCP)[9], which are more focused on critical infrastructure sectors; the standardized Cybersecurity Information Exchange Framework (CYBEX)[19]; and the Malware Information Sharing Platform (MISP)[20]; as well as proposed frameworks, like the Cybersecurity Information Exchange with Privacy (CYBEX-P), which also addresses data privacy and classified data management issues.[21]
Data sanitization[22] is one of the solutions organizations should consider using to ensure that no classified or sensitive information is disclosed to unauthorized entities while sharing CTII with external entities. In this context, an organization should carefully review and classify the information that their security appliances use and report (e.g., logs from IDS/IPS), and ensure that no information violating the organization’s policy is accidentally shared using CIE tools. For example, the CIE solution should not disclose the internal IP that has been reported by the IDS/IPS as a target of malicious activity.
Sharing of information, if not public, should be driven by agreements among the sharing parties, which address policy restrictions. Such agreements should address, among others, the following issues[23]:
- the type of information that satisfies the organization's business needs;
- the form of information exchange that is going to take place, such as emails, bulletins, documents, and automated sharing;
- the confidentiality requirements for the exchanged information and the dissemination restrictions;
- the parties authorized to access, process, and use the information;
- the technical standards used for the exchange of information to satisfy the syntactic and semantic interoperability;
- any language issues for cross-border dissemination; and
- any communication protocols and access to services.
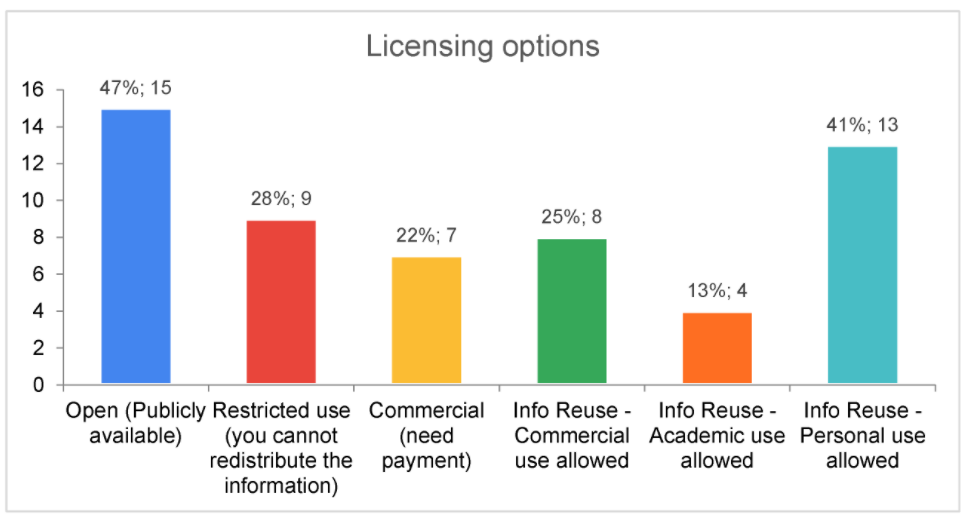
Security organizations use licensing agreements as one of the tools for controlling access to the CTII they produce and process. Several agreement schemes can be adopted by the organization, depending on its business model and needs, as well as the types of services provided to consumers and third parties. Schemes that enforce restricted use include, but are not limited to, commercial, academic or research, and personal use licenses. Other licenses may be related to information reuse options and further dissemination of this information to third parties or other communities. For example, several vendors build their own communities, where information collected by their deployed security appliances is properly analyzed, evaluated, and disseminated back to their customers.
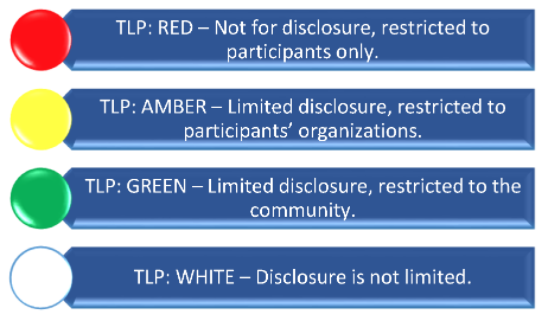
Policies can be technically supported by the use of specific protocols, such as the Traffic Light Protocol (TLP)[24] and the Information Exchange Policy (IEP)[25], which can semantically support the unambiguous transfer of policy rules among sharing parties, as explained in the following section.
Semantic and syntactic interoperability
Semantics are introduced to convey the necessary meaning for syntactically correct messages. Although sources may disseminate unstructured information that hinder data processing (such as information found on social media, news, or even on CERT and CSIRTs) in the CTII sharing process, several standards have been introduced for properly exchanging CTII among stakeholders. Compliance with standards facilitates the automated sharing of information as well as its ingestion, analysis, and integration. Although the existence of a small set of standards facilitates interoperability, adopting a wide variety of competing non-interoperable ones introduces significant overhead and can eventually hinder the exchange of information. The most prominent standards of CTII sharing are:
- 1. Structured Threat Information Expression (STIX)[26] : This OASIS-adopted standard is an information model and serialization solution used to exchange CTII. STIX 2.X is based on JSON, while its predecessors (e.g., STIX 1.X) were XML-based. STIX 1.X together with CybOX 2.X [26], a standardized language for encoding and communicating information about cyber observables, were integrated into STIX 2.0.
- 2. Malware Information Sharing and Threat Intelligence Sharing Platform (MISP)[20]: A data model composed of “events,” which usually represent threats or incidents, which in turn are composed of a list of “attributes,” such as IP addresses and domain names. Objects in MISP allow combinations of attributes and “galaxies,” which enable a deeper analysis and categorization of events.
- 3. Common Attack Pattern Enumeration and Classification (CAPEC)[27]: MITRE Corporation's CAPEC provides a comprehensive dictionary of known patterns of attack employed by adversaries to exploit known weaknesses.
- 4. Malware Attribute Enumeration and Characterization (MAEC)[28] : MITRE Corporation's GitHub-based MAEC is a structured language used for encoding and sharing information about malware based upon attributes such as behaviors, artifacts, and relationships between malware samples. It facilitates correlation, integration, and automation of malware analysis and reduces potential duplication of malware during analysis.
- 5. Managed Incident Lightweight Exchange (MILE): IETF's MILE working group develops standards to support computer and network security incident management, focusing on the definition of data formats for representing incident and indicator data, and on standardizing how application-layer protocols such as HTTPS and XMPP are utilized for sharing the structured data. Standards adopted by MILE include 1. IODEF v2 (Incident Object Description Exchange Format)[29][30], an XML-based data representation of security incident reports and indicators designed to be compatible with IDMEF (Intrusion Detection Message Exchange Format) and capable of placing an IDMEF message into incident objects; and 2. Intrusion Detection Message Exchange Format (IDMEF)[31], an XML-based data format that is used by intrusion detection and response systems to report alerts about suspicious events.
A comparison of the above CTII sharing technologies with respect to the data format and the types of data they can support is provided in Table 1.
| |||||||||||||||||||||||||||
The latest version of STIX (2.x) is defined using JSON schemas, thus rendering it easier to parse and expand than its XML-based predecessor (STIX 1.x). CAPEC is supported in both STIX 1.x, as an instance type, and STIX 2.x, as an external reference for the "attack pattern" object type.
STIX and MAEC were designed based on similar use cases. Despite their similarities, they differ in the level of description. MAEC is intended to provide a comprehensive, structured way of capturing detailed information regarding malware samples, whereas STIX is meant to capture a broad spectrum of cyber threat information, including basic information on malware in a more conceptual framework. An analysis of the types of malware-related information that can be captured by MAEC, STIX, and MAEC embedded in STIX is provided by The MITRE Corporation.[32]
STIX 2.x does not provide support for MAEC content. As a result, STIX 2.x cannot describe malware in as much detail as STIX 1.x.[33] Nevertheless, STIX 2.1 will include a new object type called "malware-analysis", which could possibly include MAEC content.[34]
Some of the aforementioned standards, such as STIX 2.0 and MISP, also support data markings which can facilitate enforcement of policies regarding the sharing of information to achieve technical and semantic interoperability. Data markings include:
- statements, e.g., copyright, terms of use, applied to the shared content; and
- Traffic Light Protocol (TLP v1.0)[24] designations.
TLP v1.0 is a set of designations used to ensure that sensitive information is shared with the appropriate audience by providing four options, as shown in Figure 3. Although optimized for human readability and person-to-person sharing and rather than automated sharing exchanges, TLP can still help restrict information sharing only with specific entities or platforms and avoid any further unnecessary or unauthorized dissemination thereof. TLP is supported by STIX 2.0 and MISP protocols.
|
TLP, however, cannot support fine-grained policies. Considering this limitation, FIRST developed the Information Exchange Policy (IEP)[25], a JSON-based framework that content producers can use to specify restrictions for threat intelligence regarding the following:
- Handling: It can be used to ensure the confidentiality of the information being shared.
- Action: It can be used to define the permitted actions or uses of the information received that can be carried out by a recipient.
- Sharing: It can be used to define any permitted redistribution of information that is received.
- Licensing: It can be used to define any applicable agreements, licenses, or terms of use that govern the information being shared.
Some of the aforementioned standards were developed to improve the sharing of cyber threat-related information, like incidents, patterns, and indicators, and not vulnerabilities, which can be considered a type of information that has its own needs and sets of standards for dissemination. Standards and languages that address vulnerabilities include:
- 1. Common Vulnerability Enumeration (CVE): A de facto standard for listing vulnerability information where each CVE entry should include a CVE ID number; a description of the vulnerability; the anticipated impact, in the form of a CVSS (Common Vulnerability Scoring System) value; and references to vulnerabilities reports and/or advisories.
- 2. Common Vulnerability Reporting Framework (CVRF)[35]: An XML-based standard that supports the creation, update, and interoperable exchange of security advisories as structured information on products, vulnerability information, and the impact and remediation statuses among interested parties. According to MITRE, CVRF allows interested parties to download the entire CVE list at once, or download CVEs for a specific year, whereas each CVE can record when it was initially published by the CVE Team, and when it was most recently modified.
- 3. Open Vulnerability and Assessment Language (OVAL): A language that can be used for representing system information, expressing specific machine states, and reporting the results of an assessment.
Technical interoperability
Technical interoperability is much related to the implementation of the necessary tools and APIs to support the automated exchange of information, which includes both consumption and delivery, as well as the support of the underlying communication protocols used for conveying CTII information. It typically involves many layers of the TCP/IP stack in formulating and transferring these messages, yet the anticipated approach towards interoperable solutions is the adoption of well-established standardized protocols that can be easily supported by the communicating parties.
Protocols that have been proposed for the transmission of CTII include the following (please note that in this paper we do not consider typical TCP/IP protocols, including those found at the application layer):
- 1. Trusted Automated Exchange of Intelligence Information (TAXII)[26]: TAXII is an application-layer protocol that is used to exchange CTII, represented in STIX, over HTTPS.
- 2. Resource-Oriented Lightweight Information Exchange (ROLIE)[36]: ROLIE defines a REST-style approach for security information publication, discovery, and sharing. Using ROLIE, security incidents, attack indicators, software vulnerabilities, configuration checklists, and other security automation information are provided as web-addressable resources. IETF’s MILE working group has drafted two extensions to ROLIE, one for CSIRTs needs[37] and another for the exchange of vulnerabilities.[38]
Other technical issues that have to be considered during sharing are related to the protection of information against unauthorized disclosure or modification, the mechanisms that are used thereof, and the corresponding cryptographic algorithms.
The CTII landscape
The CTII sharing community comprises a number of sources that disseminate information based on their respective strategy and policy. In this section, an analysis of CTII sources with respect to their interoperability characteristics is presented. This analysis focuses on the semantic standards adopted by the parties, as well as the licensing options and demonstrates the diversified approaches followed by them. Entities that want to join the CTII community or, most importantly, utilize the information provided by its members, have to consider these diversities to appropriately consume from the community or contribute to it.
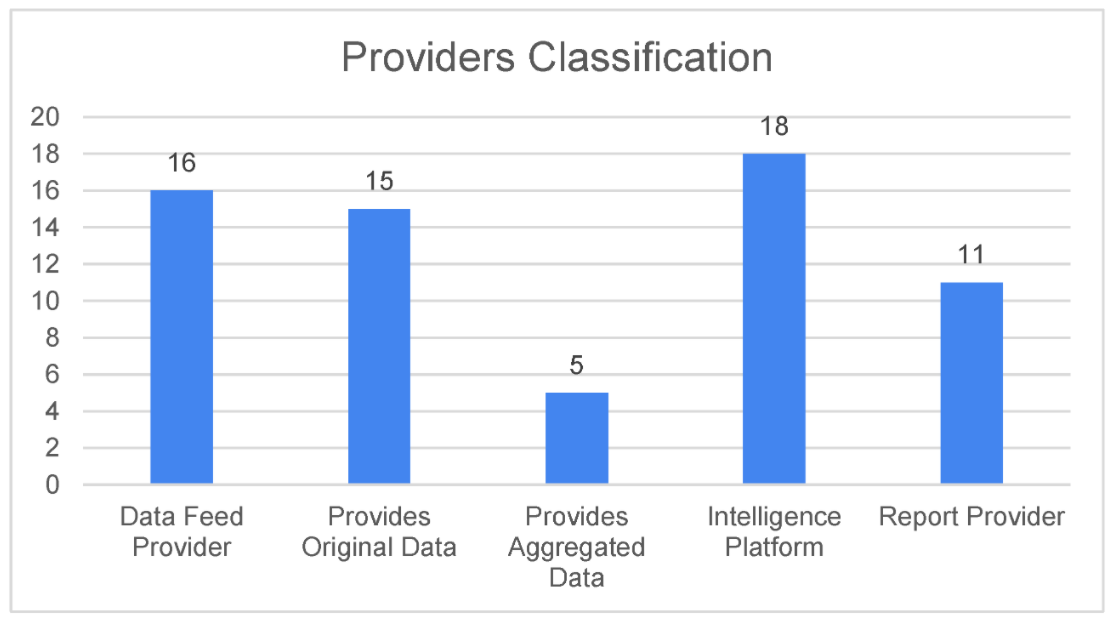
Efforts have been made to examine a large number of threat intelligence sources, including those that provide high-level information such as CERTs, and conduct an analysis on interoperability-related characteristics of 32 of them. These sources are listed in Table S1 of the Supplementary data, whereas a listing of the characteristics that were used in the analysis is provided in Table S2 of the Supplementary data. Sources providing only vulnerabilities, such as the NIST NVD, MITRE, and CVEDetails, have been excluded from this study, as the focus was more on threat sharing information, i.e., indicators, sightings, and hashes, as opposed to vulnerability sharing. Katos et al.[39] provide an extended list and analysis of those sources that provide vulnerabilities. Moreover, although an analysis of multiple National CERTs could be conducted, the authors have intentionally omitted this, as the majority of National CERTs adopt similar, if not the same approaches in information sharing. As a result, only Finland’s National CERT is included in the analysis as an example.
The 32 sources that are analyzed in this paper include original data providers, data aggregators, intelligence platforms, and report providers, the number of which is shown in Figure 4.
|
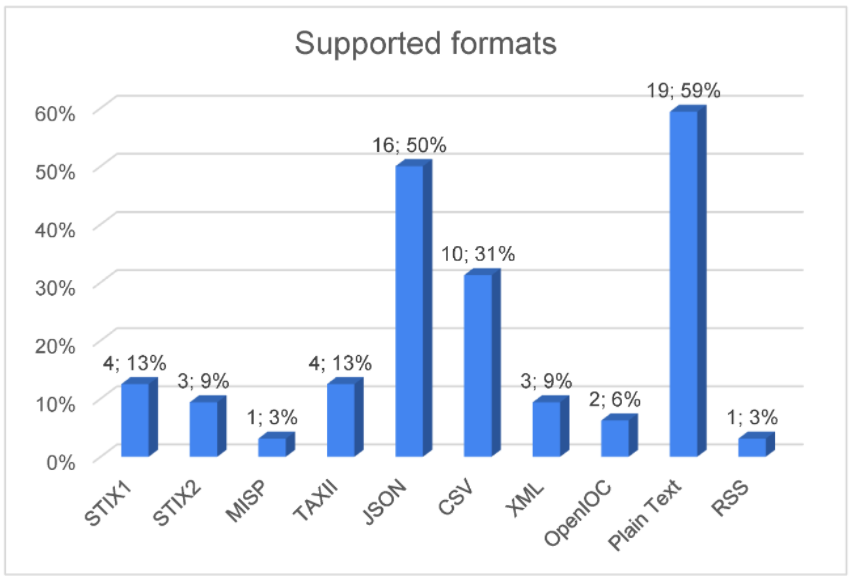
The analysis demonstrates the diversities in the CTII sharing landscape, where the majority of the sources choose to share information based on generic standards. JSON and CSV were chosen by 50% and 31% of sources, respectively, whereas another 59% of them chose plaintext, as shown in Figure 5. Unfortunately, only a small set of sources have chosen to invest on the set of CTII-oriented standards, like STIX, MISP, and OpenIOC.
|
The sources that have adopted the various formats are shown in Table 2.
| ||||||||||||||||||||||||
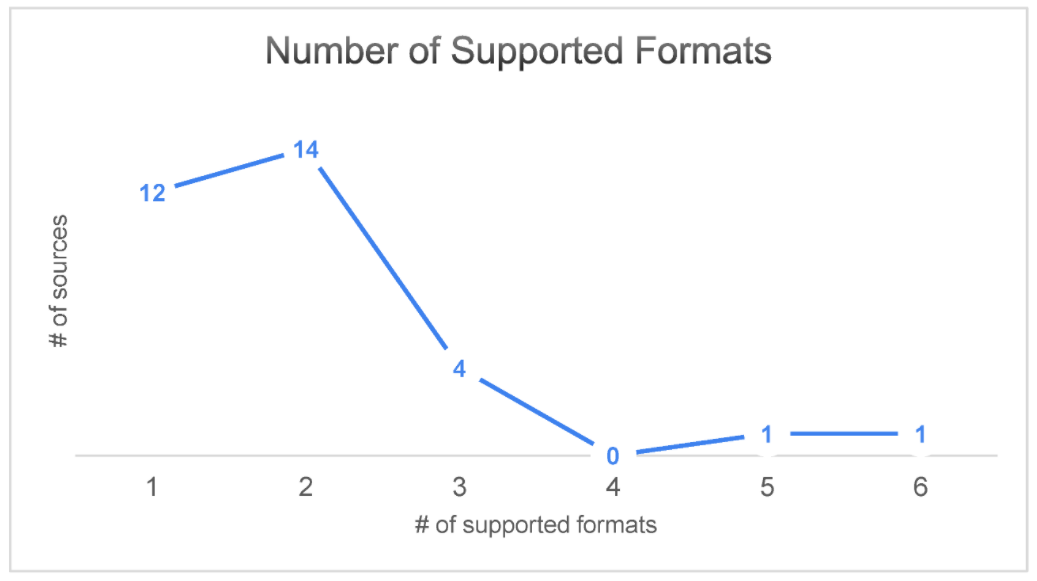
Moreover, the majority of the sources provide information only in one or two formats (as shown in Figure 6), which are generic JSON and CSV formats and not CTII sharing-related ones. This generally hinders interoperability.
|
The analysis has also demonstrated that 15 out of the 32 analyzed sources provide open, publicly available information (see Figure 7). Moreover, information reuse for personal use is allowed by 13 of them.
|
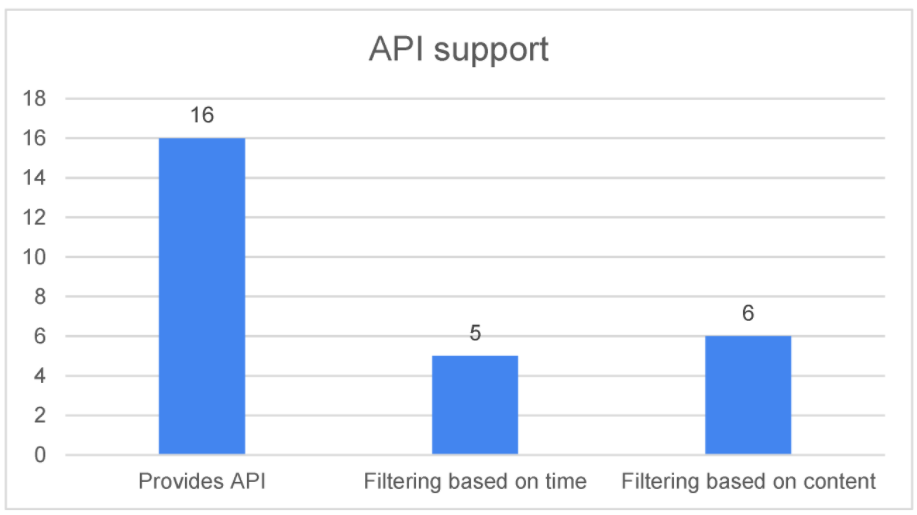
Another interesting characteristic that the analysis revealed is the number of sources that provide an API, such as REST, that can be used to easily consume the provided information, as shown in Figure 8. These sources are listed in Table 3.
|
| ||||||
Conclusions
The need for sharing information about cyber threats has been established by the cybersecurity community as a means for timely and effective protection against the aforementioned threats. The main requirements are for sharing to be performed using a structured format (so as to be machine readable and facilitate automated actions) and to have the ability to provide as much context as possible for a given threat. Nevertheless, interoperability among cyber threat sources is not related only to technical issues. This paper has proposed a layered interoperability model which addresses all those factors that can affect the exchange of cybersecurity information among stakeholders. The research conducted based on this model has proven that there is significant diversity in the way cybersecurity information gets shared by the involved sources. This approach directly impacts interoperability both from the perspectives of sharing it and/or consuming it, and also makes it harder for security analysts to effectively extract knowledge.
Future work could involve the development of an interoperability maturity model that will guide stakeholders towards the development of interoperable CTII sharing solutions, or the adaptation of their existing ones. Improving the interoperability of cybersecurity information sharing will facilitate more effective protection against cyber threats in the future.
Supplementary data
Table S1 provides a listing (in alphabetical order) of the sources that have been analysed in this work.
Table S2 provides a listing of the characteristics that have been used for the analysis that was made for the sources identified in Table S1, which adopts the approach followed by Schaberreiter et al.[18] The analysis did not consider vulnerability sharing sources. Rather, it focused on the resources that share indicators and sightings.
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Acknowledgements
Author contributions
Conceptualisation, K.R.; Data curation, A.S. and A.K.; Methodology, K.R., A.P. and C.I.; Writing—original draft, K.R. and A.P.; Writing—review & editing, C.I. and V.K. All authors have read and agreed to the published version of the manuscript.
Funding
This work has received funding from the European Research Council (ERC) under the European Union’s Horizon 2020 research and innovation program (Grant agreement Nos. 740723 and 830943).
Conflicts of interest
The funders had no role in the design of the study; in the collection, analyses, or interpretation of data; in the writing of the manuscript; or in the decision to publish the results.
References
- ↑ Accenture, Ponemon Institute (2019). "The Cost of Cybercrime" (PDF). Accenture. https://www.accenture.com/_acnmedia/pdf-96/accenture-2019-cost-of-cybercrime-study-final.pdf. Retrieved 03 March 2020.
- ↑ Kellermann, T. (5 March 2019). "Modern Bank Heists: The Bank Robbery Shifts to Cyberspace". Carbon Black. VMware, Inc. https://www.carbonblack.com/blog/modern-bank-heists-the-bank-robbery-shifts-to-cyberspace/. Retrieved 03 March 2020.
- ↑ 3.0 3.1 Johnson, C.; Badger, L.; Waltermire, D. et al. (October 2016). "Guide to Cyber Threat Information Sharing" (PDF). NIST Special Publication 800-150. National Institute of Standards and Technology. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-150.pdf. Retrieved 03 March 2020.
- ↑ 4.0 4.1 4.2 Brown, R.; Lee, R.M. (4 February 2019). "The Evolution of Cyber Threat Intelligence (CTI): 2019 SANS CTI Survey". The SANS Institute. https://www.sans.org/reading-room/whitepapers/threats/paper/38790. Retrieved 03 March 2020.
- ↑ 5.0 5.1 Tounsi, W.; Rais, H. (2018). "A survey on technical threat intelligence in the age of sophisticated cyber attacks". Computers & Security 72: 212–33. doi:10.1016/j.cose.2017.09.001.
- ↑ 6.0 6.1 "Directive (EU) 2016/1148 of the European Parliament and of the Council of 6 July 2016 concerning measures for a high common level of security of network and information systems across the Union". EUR-Lex. European Union. 6 July 2016. https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32016L1148&qid=1603749013818. Retrieved 03 March 2020.
- ↑ ETSI (October 2017). "CYBER; Implementation of the Network and Information Security (NIS) Directive" (PDF). ETSI TR 103 456 V1.1.1. https://www.etsi.org/deliver/etsi_tr/103400_103499/103456/01.01.01_60/tr_103456v010101p.pdf. Retrieved 03 March 2020.
- ↑ European Union Agency for Cybersecurity. "CSIRTs in Europe". https://www.enisa.europa.eu/topics/csirts-in-europe/csirt-inventory. Retrieved 03 March 2020.
- ↑ 9.0 9.1 Cybersecurity & Infrastructure Security Agency. "Cyber Information Sharing and Collaboration Program (CISCP)". U.S. Department of Homeland Security. https://www.cisa.gov/ciscp. Retrieved 03 March 2020.
- ↑ 10.0 10.1 Cybersecurity & Infrastructure Security Agency. "Automated Indicator Sharing". U.S. Department of Homeland Security. https://www.cisa.gov/automated-indicator-sharing-ais. Retrieved 03 March 2020.
- ↑ Office of the Director of National Intelligence (14 September 2018). "A Guide to Cyber Attribution" (PDF). https://www.dni.gov/files/CTIIC/documents/ODNI_A_Guide_to_Cyber_Attribution.pdf. Retrieved 03 March 2020.
- ↑ Chismon, D.; Ruks, M. (2015). "Threat Intelligence: Collecting, Analyzing, Evaluating" (PDF). MWR InfoSecurity Ltd. https://www.foo.be/docs/informations-sharing/Threat-Intelligence-Whitepaper.pdf. Retrieved 03 March 2020.
- ↑ ENISA (November 2014). "Actionable Information for Security Incident Response" (PDF). https://www.enisa.europa.eu/publications/actionable-information-for-security/at_download/fullReport. Retrieved 03 March 2020.
- ↑ 14.0 14.1 Burger, E.W.; Goodman, M.D.; Kampanakis, P. et al. (2014). "Taxonomy Model for Cyber Threat Intelligence Information Exchange Technologies". WISCS '14: Proceedings of the 2014 ACM Workshop on Information Sharing & Collaborative Security: 51–60. doi:10.1145/2663876.2663883.
- ↑ Skopik, F.; Settanni, G.; Fiedler, R. (2016). "A problem shared is a problem halved: A survey on the dimensions of collective cyber defense through security information sharing". Computers & Security 60: 154–76. doi:10.1016/j.cose.2016.04.003.
- ↑ "Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation)". EUR-Lex. European Union. 27 April 2016. https://eur-lex.europa.eu/legal-content/en/TXT/?uri=CELEX%3A32016R0679. Retrieved 03 March 2020.
- ↑ "ISO/IEC 27010:2015 Information technology — Security techniques — Information security management for inter-sector and inter-organizational communications". International Organization for Standardization. November 2015. https://www.iso.org/standard/68427.html. Retrieved 27 October 2020.
- ↑ 18.0 18.1 Schaberreiter, T.; Kupfersberger, V.; Rantos, K. et al. (2019). "A Quantitative Evaluation of Trust in the Quality of Cyber Threat Intelligence Sources". ARES '19: Proceedings of the 14th International Conference on Availability, Reliability and Security: 1–10. doi:10.1145/3339252.3342112.
- ↑ Rutkowski, A.; Kadobayashi, Y.; Furey, I. et al. (2010). "CYBEX: The cybersecurity information exchange framework (x.1500)". ACM SIGCOMM Computer Communication Review 40 (5): 59–64. doi:10.1145/1880153.1880163.
- ↑ 20.0 20.1 "MISP - Open Source Threat Intelligence Platform & Open Standards for Threat Information Sharing". MISP Project. https://www.misp-project.org/. Retrieved 03 March 2020.
- ↑ Sadique, F.; Bakhshaliyev, K.; Springer, J. et al. (2019). "A System Architecture of Cybersecurity Information Exchange with Privacy (CYBEX-P)". Proceedings from the 2019 IEEE 9th Annual Computing and Communication Workshop and Conference: 493–98. doi:10.1109/CCWC.2019.8666600.
- ↑ Bishop, M.; Bhumiratana, B.; Crawford, R. et al. (2004). "How to sanitize data?". Proceedings from the 13th IEEE International Workshops on Enabling Technologies: Infrastructure for Collaborative Enterprises: 217-222. doi:10.1109/ENABL.2004.36.
- ↑ "ISAO 300-2: Automating Cyber Threat Intelligence Sharing v1.0" (PDF). 5 April 2019. https://www.isao.org/storage/2019/04/ISAO-300-2-Automated-Cyber-Threat-intelligence-Sharing.pdf. Retrieved 03 March 2020.
- ↑ 24.0 24.1 FIRST. "Traffic Light Protocol (TLP)" (PDF). https://www.first.org/tlp/docs/tlp-v1.pdf. Retrieved 03 March 2020.
- ↑ 25.0 25.1 FIRST. "Information Exchange Policy (IEP)". https://www.first.org/iep/. Retrieved 03 March 2020.
- ↑ 26.0 26.1 OASIS. "OASIS Cyber Threat Intelligence (CTI) TC". https://www.oasis-open.org/committees/tc_home.php?wg_abbrev=cti. Retrieved 03 March 2020.
- ↑ MITRE Corporation (2020). "CAPEC: Common Attack Pattern Enumeration and Classification". https://capec.mitre.org/index.html. Retrieved 03 March 2020.
- ↑ MITRE Corporation (2020). "Malware Attribute Enumeraion and Characterization (MAEC)". https://maecproject.github.io/. Retrieved 03 March 2020.
- ↑ Danyliw, R. (November 2016). "The Incident Object Description Exchange Format Version 2". Internet Engineering Task Force. https://tools.ietf.org/html/rfc7970. Retrieved 03 March 2020.
- ↑ Kampanakis, P.; Suzuki, M. (November 2017). "Incident Object Description Exchange Format Usage Guidance". Internet Engineering Task Force. https://tools.ietf.org/html/rfc8274. Retrieved 03 March 2020.
- ↑ Debar, H.; Curry, D.; Feinstein, B. (March 2007). "The Intrusion Detection Message Exchange Format (IDMEF)". Internet Engineering Task Force. https://tools.ietf.org/html/rfc4765. Retrieved 03 March 2020.
- ↑ MITRE Corporation (21 April 2014). "Characterizing Malware with MAEC and STIX v 1.0" (PDF). https://stixproject.github.io/about/Characterizing_Malware_MAEC_and_STIX_v1.0.pdf. Retrieved 03 March 2020.
- ↑ OASIS (29 January 2019). "stix2-elevator Documentation Release 1.0.0" (PDF). https://stix2-elevator.readthedocs.io/_/downloads/en/v2.0.1/pdf/. Retrieved 03 March 2020.
- ↑ OASIS. "Mappings from STIX 1.x to STIX 2.x". https://stix2-elevator.readthedocs.io/en/latest/stix-mappings.html. Retrieved 03 March 2020.
- ↑ OASIS (13 September 2017). "CSAF Common Vulnerability Reporting Framework (CVRF) Version 1.2". http://docs.oasis-open.org/csaf/csaf-cvrf/v1.2/csaf-cvrf-v1.2.html. Retrieved 03 March 2020.
- ↑ Field, J.; Banghart, S.; Waltermire, D. (February 2018). "Resource-Oriented Lightweight Information Exchange (ROLIE)". Internet Engineering Task Force. https://tools.ietf.org/html/rfc8322. Retrieved 03 March 2020.
- ↑ Banghart, S.; Field, J. (5 September 2019). "Definition of ROLIE CSIRT Extension, draft-ietf-mile-rolie-csirt-05". Internet Engineering Task Force. https://tools.ietf.org/html/draft-ietf-mile-rolie-csirt-05. Retrieved 03 March 2020.
- ↑ Banghart, S. (5 September 2019). "Definition of the ROLIE Vulnerability Extension, draft-ietf-mile-rolie-vuln-02". Internet Engineering Task Force. https://tools.ietf.org/html/draft-ietf-mile-rolie-vuln-02. Retrieved 03 March 2020.
- ↑ Katos, V.; Rostami, S.; Bellonias, P. et al. (14 January 2019). "State of Vulnerabilities 2018/2019 - Analysis of Events in the life of Vulnerabilities". ENISA. doi:10.2824/139301. https://www.enisa.europa.eu/publications/technical-reports-on-cybersecurity-situation-the-state-of-cyber-security-vulnerabilities/. Retrieved 03 March 2020.
Notes
This presentation is faithful to the original, with only a few minor changes to presentation, grammar, and punctuation. In some cases important information was missing from the references, and that information was added.