Journal:Cybersecurity and privacy risk assessment of point-of-care systems in healthcare: A use case approach
| Full article title | Cybersecurity and privacy risk assessment of point-of-care systems in healthcare: A use case approach |
|---|---|
| Journal | Applied Sciences |
| Author(s) | Jofre, Marc; Navarro-Llobet, Diana; Agulló, Ramon; Puig, Jordi; Gonzalez-Granadillo, Gustavo; Zamorano, Juan M.; Romeu, Ramon |
| Author affiliation(s) | Fundació Privada Hospital Asil de Granollers, Atos Research & Innovation, Servicio Madrileño de Salud |
| Primary contact | Email: diananavarro at fphag dot org |
| Editors | Chizari, Hassan |
| Year published | 2021 |
| Volume and issue | 11(15) |
| Article # | 6699 |
| DOI | 10.3390/app11156699 |
| ISSN | 2076-3417 |
| Distribution license | Creative Commons Attribution 4.0 International |
| Website | https://www.mdpi.com/2076-3417/11/15/6699/htm |
| Download | https://www.mdpi.com/2076-3417/11/15/6699/pdf (PDF) |
Abstract
Point-of-care (POC) systems are generally used in healthcare to respond rapidly and prevent critical health conditions. Hence, POC systems often handle personal health information, and, consequently, their cybersecurity and privacy requirements are of crucial importance. However, assessing these requirements is a significant task.
In this work, we propose a use-case approach to assess specifications of cybersecurity and privacy requirements of POC systems in a structured and self-contained form. Such an approach is appropriate since use cases are one of the most common means adopted by developers to derive requirements. As a result, we detail a use case approach in the framework of a real-based healthcare IT infrastructure that includes a health information system, integration engines, application servers, web services, medical devices, smartphone apps, and medical modalities (all data simulated) together with the interaction with participants. Since our use case also sustains the analysis of cybersecurity and privacy risks in different threat scenarios, it also supports decision making and the analysis of compliance considerations.
Keywords: cybersecurity, healthcare, incidents, information privacy, IT infrastructure, point-of-care, risk assessment, sensitive medical data, threats, use case
Introduction
Cybersecurity and privacy incidents are a growing threat to the healthcare industry in general, and hospitals in particular.[1] The healthcare industry has lagged behind other industries in protecting its main stakeholders (e.g., care staff and patients), and now hospitals must invest considerable capital and effort in protecting their IT systems.[2] However, moving to more protected and resilient digital infrastructures in healthcare is a challenge because hospitals are technology-saturated, complex organizations with high end-point complexity, internal politics, and regulatory pressures. Therefore, healthcare organizations of all types looking to grow and achieve their financial, quality, service, and compliance performance objectives must understand and account for the capabilities, drivers, strategies, and challenges of other ecosystems such as cybersecurity and information privacy. Hence, as cybersecurity and privacy become more of a priority for hospitals, it is essential they holistically integrate the different processes, components, and stages influencing the healthcare ecosystem.
One relevant aspect to consider regarding cybersecurity and privacy risks are healthcare point-of-care (POC) systems which have been widely used in hospitals in order to provide innovative solutions to medical professionals. POC systems provide an overview of patients’ conditions in a way that makes it easier for professionals to respond in a timely fashion and prevent critical situations. POC platforms also incorporate medical devices and applications in order to collect, process, and visualize data. As such, large amounts of data move through POC systems, including personal health information and sensitive medical data. This data is communicated across various POC systems, backend analytical platforms, user workstations, and smartphones, demonstrating that there are multiple touch points that may cause data leakages or breaches. Naturally, these platforms create and expand attack surface, which may be challenging to fully identify and address. Hospitals and care centers need to address these threats by efficiently assessing the associated risks and mitigate them with the proper cybersecurity and privacy safeguards.
POC systems can be categorized in three classes according to their usage model: (i) testing and diagnostic applications (e.g., medical devices), (ii) patient monitoring (e.g., smartphone apps), and (iii) interfacing with other devices (e.g., web-based services and integration servers).[3] Hence, considering the latter classes, some common associated threats to POC systems encompass legacy operating systems and software, lack of timely software updates and patches, medical devices not having basic security features, insecure implementation of web-services, lack of awareness of cybersecurity and privacy issues, and limited power and resources, among others.[4] Typically, these threats and risks can be exploited by several common attack methods, including cross-site scripting, Structured Query Language (SQL) or Extensible Markup Language (XML) injection, client-side attacks, malware, and denial-of-service.
Generally, risk is defined as the combined probability of an unwanted event and its level of impact. It is described as a function of the probability that a given source of threat exerts a potential vulnerability and the consequent impact of this adverse event on the organization.[5] Cybersecurity risk, also known as information technology risk, is the new management challenge of the third millennium; it affects the information and technology assets of organizations. Sardi et al. define cybersecurity risk as “operational risks to information and technology assets that have consequences affecting the confidentiality, availability, or integrity of information or information systems.”[6] In particular, a cybersecurity threat is a potential attack that exploits a vulnerability of the system to cause damage, whilst a threat scenario is a flow of events or attacks containing interactions between a malicious actor and a system to cause damage. On the other hand, privacy risk assessment, as indicated by Wagner and Boiten[7], aims to “analyze and quantify the privacy risks associated with new systems.”
Accordingly, considerable research has been devoted to eliciting and analyzing cybersecurity and privacy risk assessment.[6][7][8][9][10] However, the applicability of these approaches in the context of cybersecurity and privacy risk assessment modeling for POC systems in healthcare ecosystems shows limitations with respect to (i) their support for explicitly specifying various types of cybersecurity threats, (ii) the definition of threat scenarios, and (iii) the specification of mitigation and preventing actions (e.g., cyber hygiene) for these threats.
Moreover, the above risks have to be properly communicated and accounted in the overall operational structure of organizations. For instance, in business, financial value may be acceptable as the ultimate unit, which is used to quantify direct cost, or even reputation and human lives. However, the healthcare sector certainly does not only operate on a competitive or financial basis, and may it prefer units that more closely relate to the concept of privacy risk. Therefore, to assess the cybersecurity requirements of POC systems, it is necessary to take into consideration the characteristics of the specific service being developed and of the device types on which the service is going to be deployed.
Accordingly, use cases are one of the most common means adopted by software engineers and end-users to elicit requirements because they ease the communication between stakeholders to assess specific requirements.[11] Additionally, to achieve widespread applicability, the need for integrating cybersecurity and privacy requirements with use case modeling warrants the development of reusable templates in different applications, and in particular for healthcare applications. Systematic approaches to eliciting cybersecurity requirements based on use cases, with emphasis on description and methods guidelines have been proposed.[12] However, existing approaches lack reusable templates for misuse cases, as opposed to only well-behaving use cases.[12][13][14][15] However, with slight modifications, use cases can aid the integration of misuse case scenarios, with functional and non-functional requirements, when considering cybersecurity and privacy risk.[16]
In the direction to remediate the limitations described above, we propose a use case approach, including misuse cases, in the framework of a real healthcare IT infrastructure for POC cybersecurity and privacy risk assessment. In particular, the objectives of this work are to (i) detail a use case that sustains the specifications of cybersecurity and privacy requirements, (ii) address the above challenges by including the modelling based on the risk management capability model (RMCM), and (iii) produce an approach tailored to accounting POC in healthcare ecosystems. In this regard, the paper is organized as follows. The next section introduces the context of our use case approach and proposed scenarios, compared to the state-of-the-art, to provide the motivations behind POC systems in healthcare. The next two sections after describe the technical developments, proposed pilot plan, and risk assessment capability for POC use cases in healthcare environments, respectively. This is followed by the penultimate section, which discusses the results connected with the outcomes in several dimensions of cybersecurity and privacy risks. The final section summarizes the work, provides conclusions, and proposes future research.
Proposed use case overview
The work presented in this article has been developed as part of a European Union (E.U.) project called the Secure and Private Health Data Exchange (CUREX)[17][18][19], which is developing a software platform aimed at delivering trust-enhancing, secure, and private-by-design systems and applications for the healthcare domain. In general, CUREX delivers specific cybersecurity and privacy risk solutions based on the following set of measurable objectives:
- deliver tools for assessing cybersecurity and privacy risks associated with health data exchange,
- deliver a decision support tool for devising optimal cybersecurity and privacy safeguards,
- deliver a blockchain-based platform for enhancing trust in health data exchange,
- enhance cyber hygiene in healthcare organizations,
- demonstrate the value of the CUREX platform through proof-of-concept use cases, and
- conduct techno-economic, market, and legal analysis and propose business and application models.
In order to accomplish these objectives, the project brings academic institutions, healthcare end-users, and software development companies together in a consortium to enhance the pool of available resources with partners and competitors to leverage technology development with high impact. Therefore, in conjunction with optimal recommended safeguards, CUREX delivers targeted measures for raising the cyber hygiene of healthcare organizations through the recommendation of strategies and methodologies for training and raising awareness activities, targeted towards healthcare employees (administration, medical, and IT personnel) on cybersecurity and privacy risks incurred during data exchange.[20] Training will involve the development of cybersecurity defending skills, e.g., empowering social engineering defenses.[21] In this way, healthcare employees will feel more confident in handling and exchanging sensitive data and improve their capabilities to perform their daily professional tasks effectively and in a secure fashion.
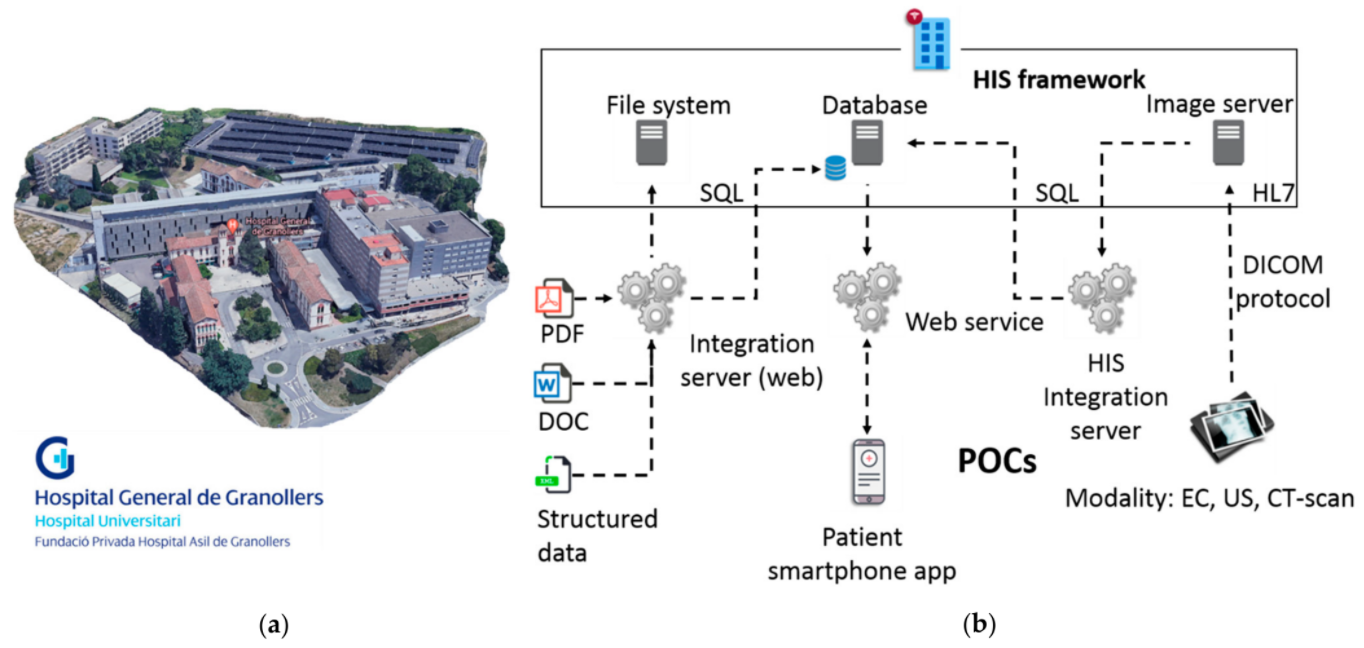
Particularly, as elucidated in the previous section, we will center this work in the development of a use case (also with misuse case extensions) to assess the cybersecurity and privacy risks in POC systems, together with remediation actions based on cyber hygiene recommendations, for different target groups of healthcare professionals at Fundació Privada Hospital Asil de Granollers (FPHAG) hospital. Contextualizing, FPHAG is a health and healthcare provider center of the public integral health system of Catalonia (SISCAT) of the Catalan health system (described in Figure 1a). The hospital provides healthcare assistance both for acute and non-acute patients, and it is the reference hospital of the territories comprising the area known as Vallès Oriental (Barcelona), serving a population of around 400,000 people with a total of 340 beds.
|
In the described context, considering data from August 2019, FPHAG’s information network infrastructure was subject to more than 6,000 different malware and intrusion attacks during a period of a year. Malware attack incidents were further classified as 205 viruses, 500 spyware, 189 adware, and 2,490 botnet attacks, whereas intrusion attack incidents’ risk levels were classified as 19 critical, 8 severe, 1,876 average, and 718 as low intensity levels. All the attacks were blocked or handled by the firewall. The latter statistics, all with positive outcome, are of relevance and effectively point out that correct infrastructure protection and IT best practices are in place at FPHAG.
While the FPHAG dealt with purely external attacks (blocked by the firewall), it's important to note that internal attacks are also very valuable to assess in a use case approach; while they are less frequent, they can produce a catastrophic outcome. Therefore, a complete independent infrastructure similar to the real IT infrastructure of the hospital has been designed and develop at FPHAG, to work with these potential attacks in a use case approach, to assess requirements for testing and improving the CUREX platform solution, as shown in Figure 1b, above. Accordingly, the developed experimental IT infrastructure is composed of:
- a health information system framework, containing file systems, a database, and an image server;
- a web integration server and services; and
- three different groups of POC systems: files of clinical history stored in the system as pdf, doc and structured data files, a patient smartphone app, and medical devices consisting of an electrocardiogram (EC), an ultrasound machine, and a CT-scan modality simulator (emulated medical device).
All the personal and health data generated and stored with the different components is simulated, hence no real data from patients has been used.
With the above-described points, the scope of the proposed use case in this work assumes the following situation:
The hospital IT department has raised concerns about the cybersecurity issues that may emerge from the operation and the communication of the clinical data handled with POC systems. Indeed, since the data contains highly sensitive personal information, it must be ensured that the hospitals’ information systems are properly maintained, and any vulnerabilities are identified and patched in a timely fashion. In addition, since the hospital has the technical capability of generating data reports and exchanging them with third parties, the platform must ensure that proper cybersecurity and privacy safeguards are in place in order to protect the integrity of the data and, most importantly, patient safety. Consequently, the hospital decides to adopt the CUREX platform in order to address these issues immediately. In conjunction with optimal recommended safeguards, CUREX delivers targeted measures for raising the cyber hygiene of healthcare organizations through the recommendation of strategies and methodologies for training and raising awareness activities, targeted towards healthcare employees (administration, medical, and IT personnel) on cybersecurity and privacy risks incurred during data exchange. Training involves the development of cybersecurity defending skills, e.g., empowering social engineering defenses. In this way, healthcare employees will feel more confident in handling and exchanging sensitive data and improve their capabilities to perform their daily professional tasks effectively and in a secure fashion.
Generally, the use case approach scope presented in this work is always with respect to POC systems' cybersecurity and privacy management, which help hospitals and care centers mitigate these risks. This becomes even more crucial when the POC systems’ data needs to be exchanged within the different services of the hospital. Therefore, the use case does not explore the contents of the health information system, but it manages the concepts of cybersecurity and privacy risk assessment together with trust—which is achieved with a shareable, verifiable, unmodifiable log in the blockchain—and cyber hygiene—which are the set of strategies and associated measures in the form of human-centric controls for raising cybersecurity and data privacy awareness of different employee groups in healthcare organizations. For this aim, three validation scenarios in the use case approach have been planned for assessing different cybersecurity and privacy situations of interest, and are described in the following subsection.
Use case validation scenarios
In this work, three scenarios are defined in a fashion similar to Sindre and Opdahl[12] for the presented use case (and also accounting for misuse cases):
- “network configuration,” where the use case scenario is not threatened by cybersecurity nor privacy risks, in order to perform an assessment in a normal operation of the use case;
- “outpatient appointment check,” where the misuse case scenario is threatened by a denial-of-service attack, which prevents legitimate users from accessing internet services, including patient access to outpatient information; and
- “visualization of clinical information,” where the misuse case scenario proposes an inside URL attack to retrieve clinical information, causing a privacy risk.
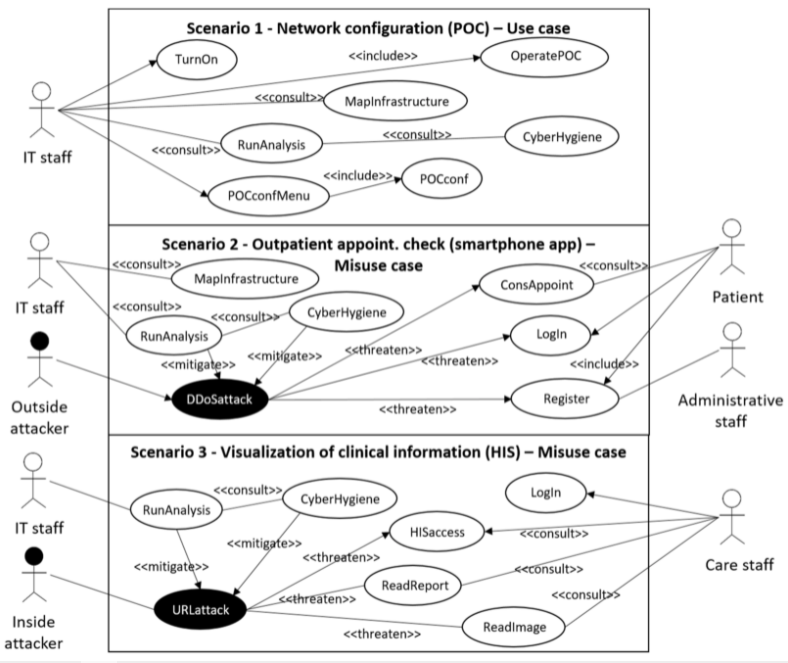
These three presented scenarios, which are focused on POC systems and dealing with cybersecurity and privacy risks in a healthcare setting, are depicted in Figure 2, and described below.
|
Scenario 1: Network configuration (POC): In this scenario, no cybersecurity attack nor information privacy leakage is simulated, but still new configurations to the IT infrastructure are simulated. In particular, it is simulated that the IT department has been requested to rearrange the IT infrastructure of the hospital, including medical devices, due to a health crisis situation, as occurred in 2020 due to the COVID-19 pandemic. For such a request, the IP/MAC address links of the medical devices pointing to the servers are modified. In this situation, the CUREX platform detects that the IP/MAC address links have been modified but no cybersecurity nor privacy risk has occurred. Therefore, the overall combined cybersecurity and privacy risk score obtained through the CUREX platform should be low.
Scenario 2: Outpatient appointment check (smartphone app): In this scenario, a distributed denial-of-service (DDOS) attack is simulated, which is considered high-risk for cybersecurity and low-risk for privacy. A participant is registered as a new simulated patient to access the simulated patient’s information through the test smartphone app, but a DDOS attack happens, resulting in the smartphone app functionality breaking down. Therefore, the participant is not able to access the information due to an out-of-service notice. In this situation, the CUREX platform has to provide a high score for cybersecurity risk and a low one for privacy risk; both values combined results in the overall value of a medium risk score reported by CUREX.
Scenario 3: Visualization of clinical information from the health information system: In this scenario, a URL-hacking cybersecurity attack with leakage of privacy information is simulated. The simulated scenario is that a participant, pretending to be a medical doctor, wants to have access to a medical image and a report of a simulated patient, but the participant intentionally accesses another patient’s data instead of the originally planned patient’s data. Therefore, the simulated cybersecurity attack also causes a privacy leakage of information, implying that both the cybersecurity and privacy information risks scores of the CUREX platform should be high.
In particular, it is of significant interest to at least pilot with Scenario 1 and either Scenario 2 or Scenario 3. Scenario 1 does not involve a cybersecurity attack but allows the CUREX toolkit to compute the cybersecurity and privacy risk when no attacks are detected. For Scenario 1, results should provide low risks to the organization and, therefore, they can continue sharing the data being requested. Conversely, the rationale behind Scenarios 2 and 3 involves simulating a cybersecurity attack and/or privacy leakage. The latter allows to assess the CUREX platform in terms of how scores change and analyze the quality of the suggested mitigation measures.
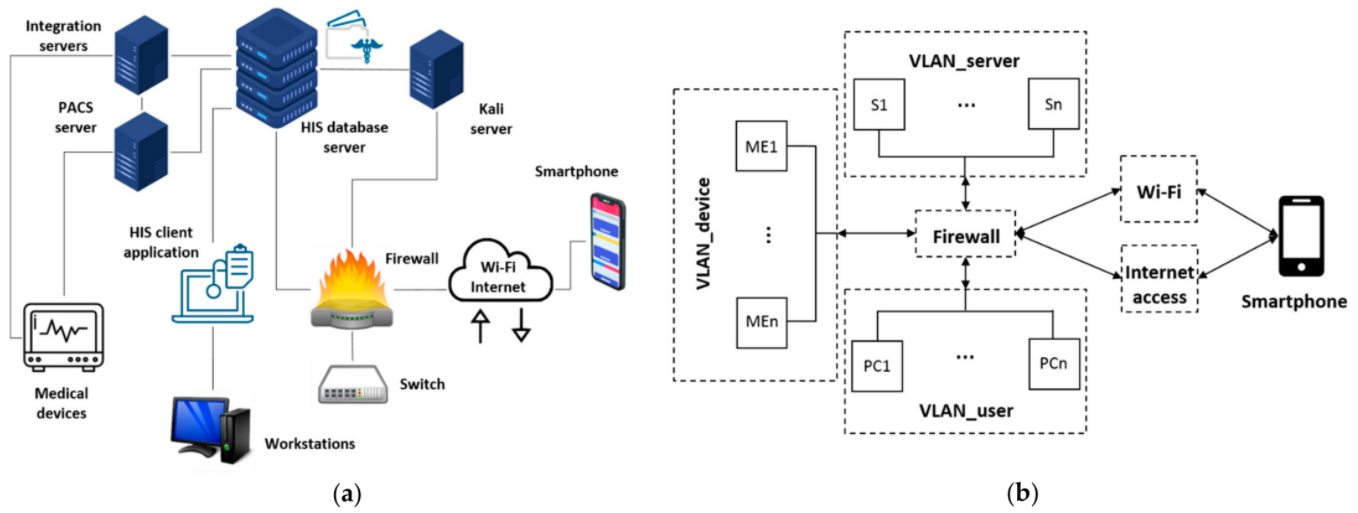
Develop technical infrastructure and CUREX tools
The technical developments for the use case proposed is a re-creation of part of the IT infrastructure of the hospital (also representative of many healthcare centers) in a pre-production environment. It is relevant that the infrastructure is developed in parallel since it is not possible to apply cybersecurity and privacy attacks and threats in a real infrastructure with real patient data and in-use equipment. Here resides one of the main points to apply use case approaches. In particular, as shown in Figure 3, the use case environment is firewall-disconnected, in any means of access, from the main infrastructure of the hospital. Therefore, the entire piloting environment is simulated but at the same time is highly representative of a real infrastructure. In particular, Figure 3a depicts the different entities composing the IT infrastructure, developed together while elucidating its logical connections to the different components. Moreover, Figure 3b shows the logical arrangement of virtual local area networks (VLANs) that consistently sectorize the different entities through the firewall hardware device. The logical arrangement consists of three VLANs, one for users to operate the workstations, another for the POC medical devices, and a third for the different servers and client applications to support the available services. Furthermore, the smartphone is connected to the use case environment through regular Wi-Fi or other internet access routes, although through a specific dedicated parallel connection channel to avoid any interference to the real infrastructure.
|
In the created environment for the use case, the workstations or PCs run under the Windows 10 operating system. The servers are placed in VMware machines, and the medical devices have different versions of Windows (e.g., Windows 7 and 10) and Linux distribution operating systems. The smartphone application to be assessed in the use case runs on a smartphone (android v9). Furthermore, several servers exist to have available integration engines, health information systems, an image server, and service integrators. Table 1 highlights the main components of the infrastructure and sectorization with VLANs.
| ||||||
Furthermore, the dedicated hardware for the use case is 8 vCPU and 48 GB RAM (servers and services installed in the infrastructure do not modify the indicated capacity values because they are accounted for outside of these values). The infrastructure is sized for 10 concurrent virtual private network (VPN) connections to allow different technical tool owners access to the use case infrastructure. Finally, different specific versions of operating systems are considered for the servers, working stations, virtual stations, smartphones, medical devices, and emulators (Windows 7, Windows 10, Linux, etc.).
Principally, the health information system is a replica of the original (implemented with the collaboration of the normal provider of maintenance and development work) but with all information cleared and only simulated images, reports, and information having been included, which were generated by the IT department. The network details of the use case infrastructure are detailed in Table 2.
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Notice that all IP and port information is safe in terms of cybersecurity and information privacy because they are not used and isolated from the real hospital’s infrastructure. Moreover, the operating systems of the workstations and PCs are selectable between Windows 7 and Windows 10, which are commonly used operating systems among health providers. Windows XP is no longer in use at the hospital facilities.
Lastly, Table 3 describes the different information that has been created or generated considering the different POC systems in the IT infrastructure, together with the technical addressable information from the smartphone application.
| |||||||||
In particular, Medical Devices 1 and 2 are not updated for clinical practice, but they operate correctly and are valid for the demonstrations. The emulated Medical Device 1 is based on the DICOM (Digital Imaging and Communication in Medicine) protocol, and it is an image viewer for biomedical imaging that was developed by the Biomedical Digital Imaging Center of UDIAT-CD S.A.[22] This emulator was developed with Java technology and can therefore be used in almost any computer and graphical operating system. Finally, the different available information from the POC systems allows for assessing the cybersecurity and privacy risk at different levels in the developed use case infrastructure, which, as described below, will be captured, processed, and analyzed by the different CUREX platform technical tools.
CUREX platform solution
The CUREX solution analyzes information coming from the monitoring infrastructure to compute cybersecurity and privacy risk scores associated to the data exchange in a health domain. CUREX has four discrete areas:
- asset and vulnerability discovery, with the goal of discovering the system’s assets and any information related to their associated vulnerabilities;
- threat intelligence, aiming to detect real-time abnormal behaviors on users, and devices, as well as anomalies in the data in order to identify new and unknown threats;
- risk management, aiming to produce risk scores and optimal safeguards towards a cyber-strategy of the healthcare organization; and
- trust enhancement, which makes use of a decentralized platform based on blockchain technology to store and share private and sensitive data, as described by University of Piraeus Research Center[17] and Diaz-Honrubia et al.[18]
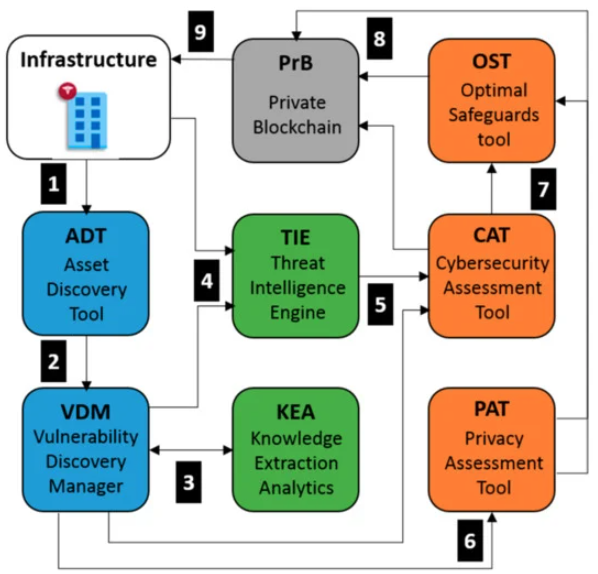
The interactions between the different tools of CUREX are depicted in Figure 4.
|
Using Scenario 3 from the prior section as an example, CUREX platform’s enumerated actions are defined in the following ordered list below, once the CUREX solution has been deployed in the infrastructure:
1. ADT scans the infrastructure and identifies the entities and resources that have direct connection with the health information system.[18] A list of assets (including IP addresses, open ports, services and/or operating systems running in each asset) is generated by the ADT and shared accordingly with other CUREX tools. It is worth noting that for this particular scenario, the ADT has discovered that some workstations are running outdated versions of the operating system (OS).
2. Upon reception of the asset list, VDM performs a vulnerability scan, using as input the list of IP addresses discovered by the ADT. As a result, VDM generates a report containing a list of security vulnerabilities associated to all the hospital’s resources (assets) detected in the network’s hospital infrastructure.[23] In particular, the VDM report contains a list of critical exploitable vulnerabilities against the outdated OS, and it is initially shared with KEA for further analysis.
3. Upon reception of the vulnerability report, KEA performs a machine learning analysis using the log events generated in the infrastructure in order to detect new threat patterns that could potentially harm the system.[24] New threat patterns are added to the VDM, which enriches the vulnerability report to be shared with other CUREX tools.
4. TIE receives the enriched vulnerability report by the VDM and in parallel, receives logs from events originated in the end user’s infrastructure. In particular, TIE employs anomaly detection and analytics to detect intrusion and malicious activities using a variety of tools and techniques. As a result, TIE is able to generate correlated alarms indicating potential threat incidents detected in the monitored infrastructure. The generated alarms are then shared with other CUREX tools for further processing and analysis. In this example, a URL-based attack is detected against one of the resources, which can potentially give unintended access to the health information system database. The generated alarms are then shared with other CUREX tools for further processing and analysis.
5. CAT receives a list of vulnerabilities from the VDM, and a list of events and alarms from TIE, which along with the risk pattern models and configuration configured by the infrastructure IT managers, provides the required input to perform a cybersecurity analysis. As a result, global and individual scores are generated, making it possible to identify critical events to assign priorities for their treatment. For each score, a set of mitigation measures is proposed by CAT. The generated CAT scores are stored in the PrB, and the list of mitigation measures is shared with OST[20] for its analysis and optimization. Regarding the considered example, one of the provided mitigation efforts provided in the generated list and selected by the IT user could be “map input values to actual filenames/URLs, etc., and reject all other inputs,” which is highly efficient and with medium associated cost of implementation.
6. In parallel, PAT also receives the vulnerability report from VDM and performs a privacy risk assessment of the organization and the platform by evaluating GDPR compliance.[25] Similar to CAT, a set of mitigation measures is proposed by PAT.[26] The generated PAT scores are stored in the PrB, and the list of mitigation measures is shared with OST for its analysis and optimization.
7. OST receives in real time the CAT and PAT mitigation measures and performs an optimal safeguard analysis based on values of costs and efficacy provided by the end user. As a result, the OST displays in its dashboard the list of mitigation measures ranked by priority. This output is also stored in the PrB.
8. PrB receives both the CAT and PAT scores and the mitigation measures from OST. CAT and PAT qualitative scores are merged, and a unified risk score is generated.
9. After the optimal mitigation measures are applied to the systems and their infrastructure by the IT end user, a new scan from the ADT will be performed and the process restarted from Step 1, finally ending with the CAT and/or PAT results that will decrease accordingly during the new risk assessment.
For all three scenarios, defined in the previous section, CUREX should provide cyber hygiene recommendations and procedures to improve the capabilities and training of participants with respect to cybersecurity and privacy risks.
Pilot plan and validation test steps
The proposed use case allows testing and evaluating cybersecurity and privacy risks, as well as for the CUREX platform potential impact on data exchange in healthcare services, focused on modelling and analyzing POC systems. First, a pilot plan has been defined in Table 4, in order to define the overall specifics involved with the use case. Notice that the defined pilot plan can be used as the base model to define other use cases in the current context, as well as in other use case models.
| ||||||||||||||||
Furthermore, following the use case diagram defined in the second section, the different validation actions of the three different scenarios have been detailed step-by-step in Table 5. Generally, the three scenarios have a common “start point” step. In this so-called STEP 0, the system is analyzed by CUREX tools, which then provide some recommendations about cybersecurity and privacy risks. Once they are implemented, it is continued with each on-demand scenario. Lastly, the execution of the different scenarios provides cyber hygiene recommendations.
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Each scenario is composed of a limited number of steps in an ordered sequence (Column 1), with clear indications of the performed action (Column 2), description of the step to perform (Column 3) and the outcome, which might be linked to a specific requirement assessment, produced by each step (Column 4). Hence, the step-by-step validation test plan described above provides sufficient information for the different participants to execute the actions required for each scenario of the use case. However, the test plan also allows the use case session managers to monitor the execution of the scenario as well as to annotate any relevant information to be further analyzed afterwards. In this way, the use case specific test plans serve as case report forms for each scenario, as described in the following section.
Discussion on risk assessment capability
There are numerous use case approaches in the literature to model cybersecurity and privacy requirements, including multilateral, unified modeling language (UML)-based, goal-oriented, problem frame-based, risk/threat analysis-based, and common criteria-based approaches.[27] In particular, the use case approach proposed in this work is based on misuse cases extending UML diagrams and relies on a form of risk/threat analysis to capture various cybersecurity and privacy risks, to elicit threat scenarios in a structured form. Furthermore, it provides mitigation recommendations relaying on a CUREX solution, or accordingly, directions given by other cybersecurity and information privacy risk assessment solutions. Therefore, the dimension of assessment capability attained in the proposed use case is large (a list of contemplated requirements allowed to be assessed are shown in Table 6).
| |||||||||||||||||||||||||||
The requirements listed in Table 6 are not particular to the CUREX solution but general to other cybersecurity and information privacy risk assessment solutions, contemplating both functional and non-functional requirements, and they can be enlarged following best-practice guidelines, privacy-by-design methodologies, and IT standards.[28] Furthermore, the described requirements regarding cybersecurity and privacy risks in Table 6 encompass some mandatory as well as optional requirements. The mandatory level is considered when the requirement is a must, without which the described functionality cannot be provided. However, the optional level is assigned when the requirement is only recommended to have an appropriate performance of the tool/service. The assigned level of mandatory requirements has been qualitatively weighted and agreed upon among different stakeholders (software developers, healthcare providers, and researchers) within the CUREX consortium. The qualitative weighting has been assigned by mapping the requirements’ urgency by the end users to the performance goals elicited by the technical development of the specific CUREX tools. Moreover, the requirements’ considerations detailed in our use case, in some part, are highly valid since they are also considered in other information risk analysis works by Williams and Woodward[4], Lin and Hsu[29], Zhang et al.[30], McFarland and Olatunbosun[31], and Wang and Jones.[32] Hence, the methodology followed can be applied to other use cases and risk assessment solutions.[33][34]
Regarding the employed assessment scoring tools, the automated cybersecurity and information privacy risks solution proposed for the use case using CUREX platform is described; however, other assessment procedures will be discussed. In particular, in the proposed use case, the cybersecurity assessment is based in employing state-of-the-art machine learning algorithms and technologies combined into an automated solution for hospitals and health care centers to understand inherent risks that emerge from exchanging health data and drive the decisions towards successfully mitigating the risks.[23] However, the information privacy risks are assessed based on the OLISTIC Enterprise risk management suites (ERMS).[26] To calculate the overall impact to all data assets of the healthcare organization, it integrates NIST’s guide for security risk assessment.[35] Nevertheless, other cybersecurity and information privacy risk assessment approaches are available, such as the common vulnerability scoring system (CVSS).[36][37] In particular, CVSS assigns severity scores (based on a formula that depends on several metrics that approximate ease of exploit and the impact) to vulnerabilities, allowing the prioritization of actions and resources according to the threats.
As directed in the detailed step-by-step use case’s scenarios of the prior section, each requirement to be assessed is introduced at a specific position of the steps to be performed by the participants. This helps with tracing the requirements along the validation test plan to ensure that the full scope of the requirements is assessed. Moreover, following an hybrid Agile-predictive methodology[38], the use case manager can decide to add or delete requirements to be assessed in the different scenarios. In this way, participants can provide specific feedback during the demonstration, validation, and evaluation of the use case through questionnaires, focus groups, and interviews. Nevertheless, the planning of the experimental protocols involves the consideration of ethical aspects[28], legal aspects[25], data usage and data processing[39], testing recruitment, and informed consent, as well as the impact of each use case and the roadmap.[40] Given this, a first validation round can be conducted to gather the participant’s results and reports to provide feedback for improving or updating the requirements in order to improve the functionality of the tools and platform solution, according to the end users' needs, beliefs, and requirements.
Importantly, usability feedback depends heavily on the subjective perceptions and the prioritization of needs of each user.[41] Therefore, it is appropriate to carry out the use case with the sufficient number of participants in order to co-create and to ground solutions that fit the final users. This is because healthcare IT decision makers will not adopt a health-related technology if it does not fulfill their current level of needs, such as security and safety, no matter how simple to use, innovative, affordable, or powerful the technology is.[42]
Furthermore, the use case proposed also places emphasis on improving cyber hygiene through the recommendation of strategies and methodologies for training and raising awareness activities for a healthcare institution’s personnel. Its validation focuses on the highly challenging condition of POC systems, spanning medical devices, big data clinical history, and smartphones (and can potentially assess other internet of things devices) through the three appropriately selected use case’s scenarios. Furthermore, the focus of the described scenarios has been placed on insider threats; as such, our use case approach easily allows personnel to develop new scenarios with other very relevant threats to healthcare, as ransomware attacks, which has proven to have had a high occurrence and a large impact in the past. In particular, one could think of a scenario where the data stored in the health information system is encrypted (e.g., by the WannaCry ransomware attack) using medical devices with legacy operating systems as entry points triggered by a participant’s misstep (which could be mounted combining Scenarios 1 and 3). Lastly, the proposed use case could be extended with security scenarios (mitigation measures) together with derivation of business continuity considerations and cost-effectiveness of the mitigation measurements.
Conclusions
This work describes a particular use case to assess cybersecurity and privacy risks for POC systems, but it can be readily generalized to other common related risk situations in healthcare. In particular, the proposed use case has been focused on allowing to experiment with the cybersecurity and privacy risk assessment for POC systems in a relevant healthcare IT infrastructure. The work presented is ambitious not only concerning the considerations regarding IT solution architectures, but also in different domains and by number of requirements that are included in the use case to be assessed. Moreover, the particular use case considerations regarding the CUREX platform can be generalized to other solution platforms and use cases, following the indications provided in the discussion section.
Furthermore, it has been argued that developing a use case approach is crucial to improving the user experience and increasing user adoption. In this regard, the designed and developed IT infrastructure contains a health information system, actual servers, POC systems, and portable devices (e.g., smartphone). Such a development forms a solid base for allowing different oriented scenarios for the participation of different stakeholders and end users to be run. This means focusing the configurations to conduct threat scenarios (misuse cases), as well as the regular functionality scenarios.
Moreover, the three specific developed use case scenarios, for cybersecurity and privacy risk assessment, have relevant differences on the outcomes in several dimensions, as well as in the adversary profiles. And an extra scenario regarding highly recurrent and impactful ransomware attacks was raised at the end of the discussion section. Although the ransomware attack has not been fully developed, the described use case approach in this work holds promise as a highly moldable tool to assess the cybersecurity and privacy risk of other threats of interest. Finally, we have also contemplated and included in the different scenarios the demonstration steps for a cybersecurity and privacy trust-enhancing platform in development (CUREX), which is part of an international research and innovation effort lead by academics, companies, and healthcare providers.
Cybersecurity and privacy protection regulations continue to expand, with more laws and regulations expected to be issued in the coming years. Therefore, it is important for healthcare providers to continue monitoring and adopting successful developments, demonstrated in validated use cases, complying with the prescribed security and privacy protection requirements, while also being aware of the applicable risks and exposures, especially for POC systems in IT health infrastructures. However, despite the increasing levels of government attention on information technology risks in healthcare and increased funding, we still need to define critical use cases—like the one proposed in this work—that can deliver the biggest impact in healthcare through cybersecurity and privacy risk assessments, further ensuring the highest quality for what is actually being delivered on the ground or showing promise in terms of developments in the pipeline.
Acknowledgements
The authors would also like to thank all the CUREX consortium members for their work: UPRC, ATOS, ALRS, CLS, INTRA, S5, LEX, 8BELLS, UBI, SURREY, UPM, UCY, AUTH, SERMAS, FPHAG and KI.
Author contributions
Conceptualization M.J. and D.N.-L.; methodology J.M.Z. and G.G.-G.; Software R.A., J.P. and R.R.; writing—original draft M.J.; validation D.N.-L., R.A., J.P., J.M.Z., G.G.-G. and R.R.; writing—review and editing D.N.-L. and R.R. All authors have read and agreed to the published version of the manuscript.
Funding
This research was funded by the European Union’s Horizon 2020 Research and Innovation Programme under Grant Agreement No. 826404.
Informed consent statement
Written informed consent was required from the participant(s) in the planned pilots.
Conflicts of interest
The authors declare no conflict of interest.
References
- ↑ Jalali, Mohammad S; Kaiser, Jessica P (28 May 2018). "Cybersecurity in Hospitals: A Systematic, Organizational Perspective" (in en). Journal of Medical Internet Research 20 (5): e10059. doi:10.2196/10059. ISSN 1438-8871. PMC PMC5996174. PMID 29807882. http://www.jmir.org/2018/5/e10059/.
- ↑ Jofre, M. (July 2020). "Holistic View Of Healthcare Cybersecurity Ecosystem". ResearchGate. doi:10.13140/RG.2.2.14306.96962. https://www.researchgate.net/publication/343722649_Holistic_View_Of_Healthcare_Cybersecurity_Ecosystem. Retrieved 21 July 2021.
- ↑ Tulasidas, Sivanesan; Mackay, Ruth; Hudson, Chris; Balachandran, Wamadeva (2017). "Security Framework for Managing Data Security within Point of Care Tests". Journal of Software Engineering and Applications 10 (02): 174–193. doi:10.4236/jsea.2017.102011. ISSN 1945-3116. http://www.scirp.org/journal/doi.aspx?DOI=10.4236/jsea.2017.102011.
- ↑ 4.0 4.1 Williams, Patricia; Woodward, Andrew (1 July 2015). "Cybersecurity vulnerabilities in medical devices: a complex environment and multifaceted problem" (in en). Medical Devices: Evidence and Research 8: 305-316. doi:10.2147/MDER.S50048. ISSN 1179-1470. PMC PMC4516335. PMID 26229513. http://www.dovepress.com/cybersecurity-vulnerabilities-in-medical-devices-a-complex-environment-peer-reviewed-article-MDER.
- ↑ Reason, J. (18 March 2000). "Human error: models and management". BMJ 320 (7237): 768–770. doi:10.1136/bmj.320.7237.768. PMC PMC1117770. PMID 10720363. https://www.bmj.com/lookup/doi/10.1136/bmj.320.7237.768.
- ↑ 6.0 6.1 Sardi, Alberto; Rizzi, Alessandro; Sorano, Enrico; Guerrieri, Anna (27 August 2020). "Cyber Risk in Health Facilities: A Systematic Literature Review" (in en). Sustainability 12 (17): 7002. doi:10.3390/su12177002. ISSN 2071-1050. https://www.mdpi.com/2071-1050/12/17/7002.
- ↑ 7.0 7.1 Wagner, Isabel; Boiten, Eerke (2018), Garcia-Alfaro, Joaquin; Herrera-Joancomartí, Jordi; Livraga, Giovanni et al.., eds., "Privacy Risk Assessment: From Art to Science, by Metrics" (in en), Data Privacy Management, Cryptocurrencies and Blockchain Technology (Cham: Springer International Publishing) 11025: 225–241, doi:10.1007/978-3-030-00305-0_17, ISBN 978-3-030-00304-3, http://link.springer.com/10.1007/978-3-030-00305-0_17. Retrieved 2021-09-01
- ↑ Hameed, Shilan S.; Hassan, Wan Haslina; Latiff, Liza Abdul; Ghabban, Fahad (23 March 2021). "A systematic review of security and privacy issues in the internet of medical things; the role of machine learning approaches" (in en). PeerJ Computer Science 7: e414. doi:10.7717/peerj-cs.414. ISSN 2376-5992. PMC PMC8022640. PMID 33834100. https://peerj.com/articles/cs-414.
- ↑ Coronado, Anthony J.; Wong, Timothy L. (1 January 2014). "Healthcare Cybersecurity Risk Management: Keys To an Effective Plan". Biomedical Instrumentation & Technology 48 (s1): 26–30. doi:10.2345/0899-8205-48.s1.26. ISSN 0899-8205. https://doi.org/10.2345/0899-8205-48.s1.26.
- ↑ Kandasamy, Kamalanathan; Srinivas, Sethuraman; Achuthan, Krishnashree; Rangan, Venkat P. (26 May 2020). "IoT cyber risk: a holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process". EURASIP Journal on Information Security 2020 (1): 8. doi:10.1186/s13635-020-00111-0. ISSN 2510-523X. https://doi.org/10.1186/s13635-020-00111-0.
- ↑ Larman, Craig. Applying UML and patterns: an introduction to object-oriented analysis and design and iterative development (3rd ed ed.). Upper Saddle River, N.J: Prentice Hall PTR, c2005. ISBN 978-0-13-148906-6.
- ↑ 12.0 12.1 12.2 12.3 Sindre, Guttorm; Opdahl, Andreas L. (24 June 2004). "Eliciting security requirements with misuse cases" (in en). Requirements Engineering 10 (1): 34–44. doi:10.1007/s00766-004-0194-4. ISSN 0947-3602. https://doi.org/10.1007/s00766-004-0194-4.
- ↑ Cockburn, Alistair (2001). Writing effective use cases. The Crystal series for software development. Boston: Addison-Wesley. ISBN 978-0-201-70225-5.
- ↑ Constantine, L.L.; Lockwood, L.A.D. (1999). Software for Use: A Practical Guide to the Models and Methods of Usage-Centered Design (1st ed.). Addison-Wesley. ISBN 9780768685305.
- ↑ Jacobson, Ivar (1992). Object-oriented software engineering: a use case driven approach. [New York] : Wokingham, Eng. ; Reading, Mass: ACM Press ; Addison-Wesley Pub. ISBN 978-0-201-54435-0.
- ↑ Yue, Tao; Briand, Lionel C.; Labiche, Yvan (4 March 2013). "Facilitating the transition from use case models to analysis models: Approach and experiments". ACM Transactions on Software Engineering and Methodology 22 (1): 5:1–5:38. doi:10.1145/2430536.2430539. ISSN 1049-331X. https://doi.org/10.1145/2430536.2430539.
- ↑ 17.0 17.1 "CUREX". University of Piraeus Research Center. 2020. https://curex-project.eu/. Retrieved 26 April 2021.
- ↑ 18.0 18.1 18.2 Diaz-Honrubia, Antonio Jesus; Rodriguez Gonzalez, Alejandro; Mora Zamorano, Juan; Rey Jiménez, Jesús; Gonzalez-Granadillo, Gustavo; Diaz, Rodrigo; Konidi, Mariza; Papachristou, Panos et al. (1 June 2019). "An Overview of the CUREX Platform". 2019 IEEE 32nd International Symposium on Computer-Based Medical Systems (CBMS): 162–167. doi:10.1109/CBMS.2019.00042. https://ieeexplore.ieee.org/document/8787402/.
- ↑ Mohammadi, Farnaz; Panou, Angeliki; Ntantogian, Christoforos; Karapistoli, Eirini; Panaousis, Emmanouil; Xenakis, Christos (14 October 2019). "CUREX: seCUre and pRivate hEalth data eXchange". IEEE/WIC/ACM International Conference on Web Intelligence - Companion Volume. WI '19 Companion (Thessaloniki, Greece: Association for Computing Machinery): 263–268. doi:10.1145/3358695.3361753. ISBN 978-1-4503-6988-6. https://doi.org/10.1145/3358695.3361753.
- ↑ 20.0 20.1 Panda, Sakshyam; Panaousis, Emmanouil; Loukas, George; Laoudias, Christos (11 January 2020). "Optimizing Investments in Cyber Hygiene for Protecting Healthcare Users". arXiv. arXiv:2001.03782v1. http://arxiv.org/abs/2001.03782.
- ↑ Jofre, M. (June 2020). "Minimum quality standard for cybersecurity training in healthcare – SecureHospitals.eu". ResearchGate. doi:10.13140/RG.2.2.17662.41289. https://www.researchgate.net/publication/343722644_Minimum_quality_standard_for_cybersecurity_training_in_healthcare_-_SecureHospitalseu. Retrieved 21 July 2021.
- ↑ Fernàndez-Bayó, Josep; Barbero, Octavio; Rubies, Carles; Sentís, Melcior; Donoso, Lluis (1 March 2000). "Distributing Medical Images with Internet Technologies: A DICOM Web Server and a DICOM Java Viewer". RadioGraphics 20 (2): 581–590. doi:10.1148/radiographics.20.2.g00mc18581. ISSN 0271-5333. https://pubs.rsna.org/doi/10.1148/radiographics.20.2.g00mc18581.
- ↑ 23.0 23.1 Gonzalez-Granadillo, G.; Diaz, R.; Veroni, E.; Xenakis, C.. "A Multi-factor Assessment Mechanism to Define Priorities on Vulnerabilities affecting Healthcare Organizations" (PDF). pp. 1–13. http://cgi.di.uoa.gr/~xenakis/Published/93-A%20Multi-factor%20Assessment%20Mechanism%20to%20Define%20Priorities%20on%20Vulnerabilities%20affecting%20Healthcare%20Organizations/VDM-CameraReady.pdf. Retrieved 26 April 2021.
- ↑ Bellas, Christos; Naskos, Athanasios; Kougka, Georgia; Vlahavas, George; Gounaris, Anastasios; Vakali, Athena; Papadopoulos, Apostolos; Biliri, Evmorfia et al. (21 July 2020). "A Methodology for Runtime Detection and Extraction of Threat Patterns" (in en). SN Computer Science 1 (5): 238. doi:10.1007/s42979-020-00226-8. ISSN 2661-8907. https://doi.org/10.1007/s42979-020-00226-8.
- ↑ 25.0 25.1 European Commission. "Data Protection". European Union. https://ec.europa.eu/info/law/law-topic/data-protection_en. Retrieved 16 May 2021.
- ↑ 26.0 26.1 Papamartzivanos, Dimitrios; Menesidou, Sofia Anna; Gouvas, Panagiotis; Giannetsos, Thanassis (2021/2). "A Perfect Match: Converging and Automating Privacy and Security Impact Assessment On-the-Fly" (in en). Future Internet 13 (2): 30. doi:10.3390/fi13020030. https://www.mdpi.com/1999-5903/13/2/30.
- ↑ "Modeling Security and Privacy Requirements: a Use Case-Driven Approach" (in en). Information and Software Technology 100: 165–182. 1 August 2018. doi:10.1016/j.infsof.2018.04.007. ISSN 0950-5849. https://www.sciencedirect.com/science/article/pii/S0950584918300703.
- ↑ 28.0 28.1 Boeckl, Katie; Fagan, Michael; Fisher, William; Lefkovitz, Naomi; Megas, Katerina N; Nadeau, Ellen; O'Rourke, Danna Gabel; Piccarreta, Ben et al. (1 June 2019). Considerations for managing Internet of Things (IoT) cybersecurity and privacy risks. Gaithersburg, MD. doi:10.6028/nist.ir.8228. https://doi.org/10.6028/NIST.IR.8228.
- ↑ Lin, Tzu-Wei; Hsu, Chien-Lung (2021/1). "FAIDM for Medical Privacy Protection in 5G Telemedicine Systems" (in en). Applied Sciences 11 (3): 1155. doi:10.3390/app11031155. https://www.mdpi.com/2076-3417/11/3/1155.
- ↑ Zhang, P.; Schmidt, D.C.; White, J.; Lenz, G. (2018). Raj, P.; Deka, G.C.. ed. "Blockchain Technology Use Cases in Healthcare" (in en). Advances in Computers 111: 1–41. doi:10.1016/bs.adcom.2018.03.006. ISSN 0065-2458. https://www.sciencedirect.com/science/article/abs/pii/S0065245818300196.
- ↑ McFarland, R.J.; Olatunbosun, S.B.O. (2020). "An Exploratory Study on the use of Internet_of_Medical_Things (IoMT) In the Healthcare Industry and their Associated Cybersecurity Risks". In Arabnia, H.R.; Deligiannidis, L.; Tinetti, F.G. (in English). Proceedings of the 2019 International Conference on Internet Computing and Internet of Things (ICOMP'19). CSREA Press. pp. 115–21. ISBN 9781601325037. http://public.eblib.com/choice/PublicFullRecord.aspx?p=6143746.
- ↑ Wang, Lidong; Jones, Randy (1 April 2019). "Big Data, Cybersecurity, and Challenges in Healthcare". 2019 SoutheastCon: 1–6. doi:10.1109/SoutheastCon42311.2019.9020632. https://ieeexplore.ieee.org/document/9020632/.
- ↑ Grguric, Andrej; Khan, Omar; Ortega-Gil, Ana; Markakis, Evangelos K.; Pozdniakov, Konstantin; Kloukinas, Christos; Medrano-Gil, Alejandro M.; Gaeta, Eugenio et al. (2021/1). "Reference Architectures, Platforms, and Pilots for European Smart and Healthy Living—Analysis and Comparison" (in en). Electronics 10 (14): 1616. doi:10.3390/electronics10141616. https://www.mdpi.com/2079-9292/10/14/1616.
- ↑ Anastasopoulou, Kalliopi; Mari, Pasquale; Magkanaraki, Aimilia; Spanakis, Emmanouil G.; Merialdo, Matteo; Sakkalis, Vangelis; Magalini, Sabina (23 September 2020). "Public and private healthcare organisations: a socio-technical model for identifying cybersecurity aspects". Proceedings of the 13th International Conference on Theory and Practice of Electronic Governance. ICEGOV 2020 (Athens, Greece: Association for Computing Machinery): 168–175. doi:10.1145/3428502.3428525. ISBN 978-1-4503-7674-7. https://doi.org/10.1145/3428502.3428525.
- ↑ NIST (2012). Guide for conducting risk assessments. Gaithersburg, MD. doi:10.6028/nist.sp.800-30r1. https://doi.org/10.6028/NIST.SP.800-30r1.
- ↑ Dugal, D.; Rich, D.. "Common Vulnerability Scoring System SIG". FIRST.org. Forum of Incident Response and Security Teams, Inc. https://www.first.org/cvss/. Retrieved 17 July 2021.
- ↑ Nikoloudakis, Y. (2019). "A Universal Cyber Security Toolkit for Health-Care Industry" (PDF). D3.3 - Vulnerability Assessment as a Service v1. SPHINX Consortium. https://ec.europa.eu/research/participants/documents/downloadPublic?documentIds=080166e5d0ebe11a&appId=PPGMS. Retrieved 16 July 2021.
- ↑ Agile Alliance (2017). "Agile Practice Guide". Project Management Institute. https://www.pmi.org/pmbok-guide-standards/practice-guides/agile. Retrieved 17 May 2021.
- ↑ Azarm-Daigle, M.; Kuziemsky, C.; Peyton, L. (1 January 2015). "A Review of Cross Organizational Healthcare Data Sharing" (in en). Procedia Computer Science 63: 425–432. doi:10.1016/j.procs.2015.08.363. ISSN 1877-0509. https://www.sciencedirect.com/science/article/pii/S1877050915024989.
- ↑ Vanclay, Frank (1 March 2003). "International Principles For Social Impact Assessment". Impact Assessment and Project Appraisal 21 (1): 5–12. doi:10.3152/147154603781766491. ISSN 1461-5517. https://doi.org/10.3152/147154603781766491.
- ↑ Petrie, Helen; Bevan, Nigel (11 June 2009), "The Evaluation of Accessibility, Usability, and User Experience", Human Factors and Ergonomics (CRC Press): 1–16, doi:10.1201/9781420064995-c20, https://doi.org/10.1201/9781420064995-c20. Retrieved 2021-09-03
- ↑ Alrahbi, Dana; Khan, Mehmood; Hussain, Matloub (2 January 2021). "Exploring the motivators of technology adoption in healthcare". International Journal of Healthcare Management 14 (1): 50–63. doi:10.1080/20479700.2019.1607451. ISSN 2047-9700. https://doi.org/10.1080/20479700.2019.1607451.
Notes
This presentation is faithful to the original, with only a few minor changes to presentation, grammar, and punctuation. In some cases important information was missing from the references, and that information was added. The original citation 37 is to Wikipedia, which is frowned upon; in this version, a URL to the actual CVSS site was substituted instead.